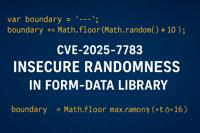
CVE-2025-7783
Usage of unsafe random function in form-data for choosing boundary
Description
Use of Insufficiently Random Values vulnerability in form-data allows HTTP Parameter Pollution (HPP). This vulnerability is associated with program files lib/form_data.Js. This issue affects form-data: < 2.5.4, 3.0.0 - 3.0.3, 4.0.0 - 4.0.3.
INFO
Published Date :
July 18, 2025, 5:15 p.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
7ffcee3d-2c14-4c3e-b844-86c6a321a158
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 4.0 | CRITICAL | 7ffcee3d-2c14-4c3e-b844-86c6a321a158 |
Solution
- Update form-data to version 2.5.4 or later.
- Update form-data to version 3.0.4 or later.
- Update form-data to version 4.0.4 or later.
Public PoC/Exploit Available at Github
CVE-2025-7783 has a 16 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-7783.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-7783 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-7783
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
HCL Dockerfile Java HTML CSS JavaScript
An agentic approach to triage ACS_CVSS_CRITICAL JIRA tickets
Python
None
Mirror of https://github.com/nomi-sec/PoC-in-GitHub
A DevSecOps CI/CD pipeline implementation using Jenkins, Docker-in-Docker, and Trivy. Automates container security auditing by scanning images for CVEs and enforcing build failure on critical vulnerabilities.
Dockerfile JavaScript Nix
None
Dockerfile Makefile TypeScript JavaScript Shell
None
None
TypeScript JavaScript
None
Python Shell JavaScript HTML CSS
POC of CVE-2025-7783
JavaScript Python
None
HTML JavaScript
CVEs assigned by the Harborist CNA.
A backstage extension for Quarkus
quarkus-extension
Makefile Java JavaScript Shell TypeScript HTML Dockerfile
A template to quickly set up demos or lightweight focus projects
HTML CSS TypeScript
Demo task react checkers with auto-play for Tesla, Nov 2020
HTML CSS TypeScript
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-7783 vulnerability anywhere in the article.

-
Daily CyberSecurity
“Fiber” Optic Failure: Predictable UUIDs Expose Go Web Framework to Hijacking
A critical vulnerability has been uncovered in Fiber, the high-performance web framework for Go that powers countless modern web applications. The flaw, tracked as CVE-2025-66630, carries a CVSS score ... Read more

-
Daily CyberSecurity
Critical Axios Flaw (CVE-2025-54371) in Form-Data Dependency Exposes Millions to HTTP Manipulation
Axios, the popular promise-based HTTP client for Node.js and browsers, has been found vulnerable through a critical flaw in a transitive dependency, putting millions of applications at risk of multipa ... Read more

-
CybersecurityNews
Critical Vulnerability in JavaScript Library Exposes Millions of Apps to Code Execution Attacks
A critical security vulnerability has been discovered in the widely-used JavaScript form-data library, potentially exposing millions of applications to code execution attacks. The vulnerability, assig ... Read more
-
Daily CyberSecurity
Critical Flaw (CVE-2025-7783, CVSS 9.4) in Form-Data Library Exposes Millions of Apps to Multipart Injection & RCE
A critical vulnerability has been uncovered in the widely used JavaScript library Form-Data, impacting millions of applications that rely on it to submit form data and file uploads. Tracked as CVE-202 ... Read more

-
Daily CyberSecurity
Microsoft: China-Backed APTs Actively Exploiting SharePoint Flaws (CVE-2025-49704 & CVE-2025-49706)
Last week, the Microsoft Security Response Center (MSRC) issued an urgent advisory regarding active exploitation of critical vulnerabilities in on-premises SharePoint Server installations. The alert, ... Read more
The following table lists the changes that have been made to the
CVE-2025-7783 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 03, 2025
Action Type Old Value New Value Added Reference https://lists.debian.org/debian-lts-announce/2025/07/msg00023.html -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Jul. 22, 2025
Action Type Old Value New Value Added Reference https://github.com/form-data/form-data/security/advisories/GHSA-fjxv-7rqg-78g4 -
New CVE Received by 7ffcee3d-2c14-4c3e-b844-86c6a321a158
Jul. 18, 2025
Action Type Old Value New Value Added Description Use of Insufficiently Random Values vulnerability in form-data allows HTTP Parameter Pollution (HPP). This vulnerability is associated with program files lib/form_data.Js. This issue affects form-data: < 2.5.4, 3.0.0 - 3.0.3, 4.0.0 - 4.0.3. Added CVSS V4.0 AV:N/AC:H/AT:N/PR:N/UI:N/VC:H/VI:H/VA:N/SC:H/SI:H/SA:N/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:X/AU:X/R:X/V:X/RE:X/U:X Added CWE CWE-330 Added Reference https://github.com/form-data/form-data/commit/3d1723080e6577a66f17f163ecd345a21d8d0fd0 Added Reference https://github.com/form-data/form-data/security/advisories/GHSA-fjxv-7rqg-78g4