CVE-2026-5358
Static buffer overflow in deprecated nis_local_principal
Description
Rejected reason: REJECTED: CVE-2026-5358 is rejected for two reasons. Firstly it has been discovered that no NIS+ client or server was ever released for any Linux-based OS distributions and as such this makes the API provisional and unused. Secondly it has been discovered that the NIS+ cold start cache (/var/nis/NIS_COLD_START) cannot be bypassed and as such the API can only be called with a trusted server from the pre-populated cache. The use of a trusted server means no trust boundary is crossed and this is therefore considered a normal bug.
INFO
Published Date :
April 20, 2026, 9:16 p.m.
Last Modified :
April 22, 2026, 2:17 p.m.
Remotely Exploit :
Yes !
Source :
3ff69d7a-14f2-4f67-a097-88dee7810d18
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Port applications away from NIS.
- Update the GNU C Library.
- Remove NIS support if not needed.
Public PoC/Exploit Available at Github
CVE-2026-5358 has a 1 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
This project provides a simple example of Spring Boot CRUD application with Postgres DB, docker-compose and LGTM Observability support
docker docker-compose grafana jdbc lgtm-stack makefile postgres spring-boot
Makefile Shell Dockerfile Java
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2026-5358 vulnerability anywhere in the article.
-
Daily CyberSecurity
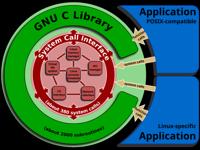
Three Silent Vulnerabilities Discovered in the glibc Core
The core of many Linux-based operating systems is facing a series of security challenges. Recent advisories for the GNU C Library (glibc) have disclosed three distinct vulnerabilities ranging from hea ... Read more
The following table lists the changes that have been made to the
CVE-2026-5358 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Rejected by 3ff69d7a-14f2-4f67-a097-88dee7810d18
Apr. 22, 2026
Action Type Old Value New Value -
CVE Modified by 3ff69d7a-14f2-4f67-a097-88dee7810d18
Apr. 22, 2026
Action Type Old Value New Value Changed Description The obsolete nis_local_principal function in the GNU C Library version 2.43 and older may overflow a buffer in the data section, which could allow an attacker to spoof a crafted response to a UDP request generated by this function and overwrite neighboring static data in the requesting application. NIS support is obsolete and has been deprecated in the GNU C Library since version 2.26 and is only maintained for legacy usage. Applications should port away from NIS to more modern identity and access management services. Rejected reason: REJECTED: CVE-2026-5358 is rejected for two reasons. Firstly it has been discovered that no NIS+ client or server was ever released for any Linux-based OS distributions and as such this makes the API provisional and unused. Secondly it has been discovered that the NIS+ cold start cache (/var/nis/NIS_COLD_START) cannot be bypassed and as such the API can only be called with a trusted server from the pre-populated cache. The use of a trusted server means no trust boundary is crossed and this is therefore considered a normal bug. Removed CVSS V3.1 CISA-ADP: AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:H/A:H Removed CWE GNU C Library: CWE-120 Removed Reference GNU C Library: https://sourceware.org/bugzilla/show_bug.cgi?id=34067 Removed Reference CISA-ADP: https://sourceware.org/bugzilla/show_bug.cgi?id=34067 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Apr. 21, 2026
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:H/A:H Added Reference https://sourceware.org/bugzilla/show_bug.cgi?id=34067 -
New CVE Received by 3ff69d7a-14f2-4f67-a097-88dee7810d18
Apr. 20, 2026
Action Type Old Value New Value Added Description The obsolete nis_local_principal function in the GNU C Library version 2.43 and older may overflow a buffer in the data section, which could allow an attacker to spoof a crafted response to a UDP request generated by this function and overwrite neighboring static data in the requesting application. NIS support is obsolete and has been deprecated in the GNU C Library since version 2.26 and is only maintained for legacy usage. Applications should port away from NIS to more modern identity and access management services. Added CWE CWE-120 Added Reference https://sourceware.org/bugzilla/show_bug.cgi?id=34067