CVE-2024-10957
UpdraftPlus: WP Backup & Migration Plugin 1.23.8 - 1.24.11 - Unauthenticated PHP Object Injection
Description
The UpdraftPlus: WP Backup & Migration Plugin plugin for WordPress is vulnerable to PHP Object Injection in all versions from 1.23.8 to 1.24.11 via deserialization of untrusted input in the 'recursive_unserialized_replace' function. This makes it possible for unauthenticated attackers to inject a PHP Object. No known POP chain is present in the vulnerable software, which means this vulnerability has no impact unless another plugin or theme containing a POP chain is installed on the site. If a POP chain is present via an additional plugin or theme installed on the target system, it may allow the attacker to perform actions like delete arbitrary files, retrieve sensitive data, or execute code depending on the POP chain present. An administrator must perform a search and replace action to trigger the exploit.
INFO
Published Date :
Jan. 4, 2025, 2:15 p.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
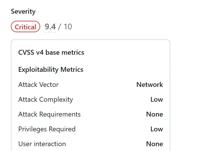
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Update the UpdraftPlus plugin to the latest version.
- Review and update other installed plugins and themes.
- Monitor for any suspicious activity after updates.
Public PoC/Exploit Available at Github
CVE-2024-10957 has a 1 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-10957.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-10957 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-10957
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
WordPress vulnerability scanner with public exploit/POC lookup, gambling spam (judol) detection, and AI-powered analysis. Scan plugins, themes & core for known CVEs — offline or remote.
cisa-kev cli cve exploit gambling judol pentesting-tools security-audit wordpress wordpress-security wordpress-security-scanner wp-scan
Python PHP Shell HTML
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-10957 vulnerability anywhere in the article.

-
TheCyberThrone
TheCyberThrone Security Weekly Review – January 11, 2025
Welcome to TheCyberThrone cybersecurity week in review will be posted covering the important security happenings. This review is for the week ending Saturday, January 11, 2025.Redis was affected by CV ... Read more

-
TheCyberThrone
Moxa Routers was affected by critical vulnerabilities
IntroductionIn the realm of cybersecurity, vulnerabilities in network devices can have severe consequences, potentially exposing systems to unauthorized access and malicious attacks. Two critical vuln ... Read more

-
TheCyberThrone
CISA KEV UPDATE Part I – January 2025
The US CISA has added 3 vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog based on the evidence of active exploitation.CVE-2024-41713: Mitel MiCollab Path Traversal VulnerabilityDe ... Read more

-
TheCyberThrone
Redis was affected by CVE-2024-51741 and CVE-2024-46981
CVE-2024-51741Description:This vulnerability affects Redis, an open-source in-memory data structure store used as a database, cache, and message broker. The issue arises when an authenticated user wit ... Read more

-
TheCyberThrone
CVE-2024-10957: UpdraftPlus WordPress Plugin Vulnerability
CVE-2024-10957 is a high-severity vulnerability affecting the UpdraftPlus: WP Backup & Migration Plugin for WordPress. This vulnerability, present in versions up to and including 1.24.11, enables atta ... Read more
-
Cybersecurity News
GoCD Patches Critical Vulnerability Allowing User Privilege Escalation
Open-source CI/CD platform GoCD has released an urgent security update to address a critical vulnerability that could allow malicious authenticated users to escalate their privileges to administrator ... Read more

-
Cybersecurity News
Cybersecurity Alert: FireScam—The Android Malware Disguised as Telegram Premium
In an era where mobile applications dominate daily life, cybersecurity threats have reached unprecedented sophistication. A recent report by CYFIRMA unveils FireScam, a dangerous Android malware masqu ... Read more

-
Cybersecurity News
CVE-2024-10957 Exposes Over 3 Million WordPress Sites to Unauthenticated PHP Object Injection Exploits
A newly discovered vulnerability in the UpdraftPlus Backup & Migration Plugin, used by over 3 million WordPress websites globally, has raised significant security concerns. Identified as CVE-2024-1095 ... Read more
The following table lists the changes that have been made to the
CVE-2024-10957 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by [email protected]
Jan. 06, 2025
Action Type Old Value New Value Changed Description The UpdraftPlus: WP Backup & Migration Plugin plugin for WordPress is vulnerable to PHP Object Injection in all versions up to, and including, 1.24.11 via deserialization of untrusted input in the 'recursive_unserialized_replace' function. This makes it possible for unauthenticated attackers to inject a PHP Object. No known POP chain is present in the vulnerable software. If a POP chain is present via an additional plugin or theme installed on the target system, it could allow the attacker to delete arbitrary files, retrieve sensitive data, or execute code. An administrator must perform a search and replace action to trigger the exploit. The UpdraftPlus: WP Backup & Migration Plugin plugin for WordPress is vulnerable to PHP Object Injection in all versions from 1.23.8 to 1.24.11 via deserialization of untrusted input in the 'recursive_unserialized_replace' function. This makes it possible for unauthenticated attackers to inject a PHP Object. No known POP chain is present in the vulnerable software, which means this vulnerability has no impact unless another plugin or theme containing a POP chain is installed on the site. If a POP chain is present via an additional plugin or theme installed on the target system, it may allow the attacker to perform actions like delete arbitrary files, retrieve sensitive data, or execute code depending on the POP chain present. An administrator must perform a search and replace action to trigger the exploit. -
New CVE Received by [email protected]
Jan. 04, 2025
Action Type Old Value New Value Added Description The UpdraftPlus: WP Backup & Migration Plugin plugin for WordPress is vulnerable to PHP Object Injection in all versions up to, and including, 1.24.11 via deserialization of untrusted input in the 'recursive_unserialized_replace' function. This makes it possible for unauthenticated attackers to inject a PHP Object. No known POP chain is present in the vulnerable software. If a POP chain is present via an additional plugin or theme installed on the target system, it could allow the attacker to delete arbitrary files, retrieve sensitive data, or execute code. An administrator must perform a search and replace action to trigger the exploit. Added CVSS V3.1 AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H Added CWE CWE-502 Added Reference https://plugins.trac.wordpress.org/browser/updraftplus/trunk/includes/class-search-replace.php#L411 Added Reference https://plugins.trac.wordpress.org/changeset/3212299/ Added Reference https://www.wordfence.com/threat-intel/vulnerabilities/id/4729ed37-96b2-4717-8a72-89b9a21ec058?source=cve