CVE-2024-23113
Fortinet Multiple Products Format String Vulnerability - [Actively Exploited]
Description
A use of externally-controlled format string in Fortinet FortiOS versions 7.4.0 through 7.4.2, 7.2.0 through 7.2.6, 7.0.0 through 7.0.13, FortiProxy versions 7.4.0 through 7.4.2, 7.2.0 through 7.2.8, 7.0.0 through 7.0.14, FortiPAM versions 1.2.0, 1.1.0 through 1.1.2, 1.0.0 through 1.0.3, FortiSwitchManager versions 7.2.0 through 7.2.3, 7.0.0 through 7.0.3 allows attacker to execute unauthorized code or commands via specially crafted packets.
INFO
Published Date :
Feb. 15, 2024, 2:15 p.m.
Last Modified :
Oct. 24, 2025, 12:54 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Fortinet FortiOS, FortiPAM, FortiProxy, and FortiWeb contain a format string vulnerability that allows a remote, unauthenticated attacker to execute arbitrary code or commands via specially crafted requests.
Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
Unknown
https://www.fortiguard.com/psirt/FG-IR-24-029 ; https://nvd.nist.gov/vuln/detail/CVE-2024-23113
Affected Products
The following products are affected by CVE-2024-23113
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Upgrade to Fortigate version 7.0.14 / 7.2.7 / 7.4.3 or later.
Public PoC/Exploit Available at Github
CVE-2024-23113 has a 35 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-23113.
| URL | Resource |
|---|---|
| https://fortiguard.com/psirt/FG-IR-24-029 | Vendor Advisory |
| https://fortiguard.com/psirt/FG-IR-24-029 | Vendor Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-23113 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-23113 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-23113
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
A proof of concept for CVE 2024 23113 inspired by WatchTowr's article.
Python
A python based passive and active security scanner
Python HTML
None
None
Dockerfile Python
None
This python scripts searches a client list to see if their FortiGate device is vulnerable to this CVE.
Python
None
HTML Python Shell
A collection of Vulnerability Research and Reverse Engineering writeups.
CVE-2024-23113 是一个在 Linux Kernel 中被发现的漏洞,它属于 任意代码执行漏洞,影响了 bpf (Berkeley Packet Filter) 子系统。具体来说,这个漏洞影响了 bpf 程序的 bpf_prog 类型的对象,并且可以允许攻击者通过构造恶意的 BPF 程序来在内核空间执行恶意代码。
Python
A curated collection of CVE exploitation proof-of-concept (POC) codes and resources. This repository is designed for security researchers, ethical hackers, and enthusiasts to study and understand various CVE vulnerabilities and their exploitation methods. Always ensure responsible usage for educational and ethical purposes only.
CVE-2024-23113 是一个严重的安全漏洞,影响 Fortinet 的多款产品,包括 FortiOS、FortiProxy、FortiPAM 和 FortiSwitchManager。该漏洞允许未经身份验证的远程攻击者通过特制的请求,在受影响的设备上执行任意代码或命令,可能导致系统被完全控制。
cve exp poc rce
Python
None
FortiManager Unauthenticated Remote Code Execution (CVE-2024-47575)
Python
Fortinet Fortimanager Unauthenticated Remote Code Execution AKA FortiJump CVE-2024-47575
Python
POC TO RCE
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-23113 vulnerability anywhere in the article.

-
TheCyberThrone
CISA adds CVE-2025-53770 SharePoint Vulnerability to KEV
July 21, 2025SummaryA critical remote code execution (RCE) vulnerability has been discovered in Microsoft SharePoint Server (on-premises versions only). The vulnerability, tracked as CVE-2025-53770, a ... Read more

-
Cybersecurity News
CVE-2024-50330 (CVSS 9.8): Unpatched Ivanti Endpoint Manager Vulnerable to RCE Attacks
Software company Ivanti has released urgent security updates for its Endpoint Manager to address a range of vulnerabilities, including several that could allow for remote code execution (RCE).The vuln ... Read more

-
Cybersecurity News
CVE-2024-8068 & CVE-2024-8069: Citrix Session Recording Manager Unauthenticated RCE Exploits Publicly Available
Security researchers at watchTowr have uncovered two critical vulnerabilities in Citrix Session Recording Manager that, when chained together, allow unauthenticated remote code execution (RCE) on Citr ... Read more

-
Cybersecurity News
CVE-2024-44102 (CVSS 10) Found in Siemens TeleControl Server Basic: Urgent Update Required
A critical security vulnerability has been discovered in Siemens TeleControl Server Basic V3.1, a software solution used for remote monitoring and control of industrial plants. The vulnerability, iden ... Read more

-
Cybersecurity News
CVE-2024-11068 (CVSS 9.8): Critical D-Link DSL-6740C Flaw, Immediate Replacement Advised
TWCERT/CC has issued multiple security advisories for the D-Link DSL-6740C modem, revealing a range of severe vulnerabilities that could expose users to remote attacks.The modem, which is no longer su ... Read more

-
Cybersecurity News
JavaScript Drive-By Attacks: New Exploits without 0-Day in Google Chrome
Ron Masas from Imperva Threat Research has uncovered a new way attackers can target Chrome users without relying on 0-day vulnerabilities. This approach leverages the File System Access API, which all ... Read more

-
Cybersecurity News
ZoneMinder’s CVE-2024-51482: A 10/10 Severity Vulnerability Exposes SQL Databases
A newly identified security vulnerability in ZoneMinder, a popular open-source video surveillance platform, could allow attackers to gain control over SQL databases, compromising data confidentiality ... Read more

-
The Cyber Express
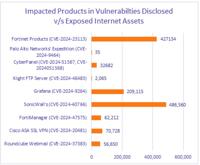
New Vulnerabilities in Fortinet, SonicWall, and Grafana Pose Significant Risks
Cyble Research and Intelligence Labs (CRIL) has identified new IT vulnerabilities affecting Fortinet, SonicWall, Grafana Labs, and CyberPanel, among others. The report for the week of October 23-29 hi ... Read more

-
Cybersecurity News
MediaTek Security Bulletin Highlights High Severity Vulnerabilities in Mobile Chipsets
MediaTek, a leading global fabless semiconductor company, has issued a security bulletin disclosing multiple vulnerabilities across its chipset product line. These vulnerabilities impact a range of de ... Read more
-
The Cyber Express
Nearly 1 Million Vulnerable Fortinet, SonicWall Devices Exposed to the Web
Nearly 1 million Fortinet and SonicWall devices with actively exploited vulnerabilities are exposed on the internet, according to Cyble’s weekly vulnerability report published today. The report also l ... Read more

-
TheCyberThrone
The CyberThrone Most Exploited Vulnerabilities Top 10 – October 2024
Welcome to TheCyberThrone most exploited vulnerabilities review. This review is for the month of October 2024CVE-2024-21762: Fortinet FortiOS: Out-of-bounds WriteCVSS 3.1 score : 9.8 CISA KEV : Y ... Read more

-
The Register
Warning! FortiManager critical vulnerability under active attack
Fortinet has gone public with news of a critical flaw in its software management platform. The security vendor apparently began informing customers privately about the issue a few days ago but has sin ... Read more

-
Cybersecurity News
Fortinet Warns of Actively Exploited Flaw in FortiManager: CVE-2024-47575 (CVSS 9.8)
Fortinet has issued a security advisory for its FortiManager platform, addressing a critical vulnerability—CVE-2024-47575—which has been actively exploited in the wild. This vulnerability, rated at CV ... Read more

-
The Hacker News
CISA Adds ScienceLogic SL1 Vulnerability to Exploited Catalog After Active Zero-Day Attack
Vulnerability / Cyber Threat The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a critical security flaw impacting ScienceLogic SL1 to its Known Exploited Vulnerabilities ... Read more

-
Help Net Security
Fortinet releases patches for undisclosed critical FortiManager vulnerability
In the last couple of days, Fortinet has released critical security updates for FortiManager, to fix a critical vulnerability that is reportedly being exploited by Chinese threat actors. Security upda ... Read more

-
The Hacker News
THN Cybersecurity Recap: Top Threats, Tools and News (Oct 14 - Oct 20)
Cybersecurity / Weekly Recap Hi there! Here's your quick update on the latest in cybersecurity. Hackers are using new tricks to break into systems we thought were secure—like finding hidden doors in l ... Read more

-
Help Net Security
Week in review: 87k+ Fortinet devices still open to attack, red teaming tool used for EDR evasion
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: 87,000+ Fortinet devices still open to attack, are yours among them? (CVE-2024-23113) Last week, CISA ... Read more

-
Cybersecurity News
CVE-2024-45216: Critical Authentication Bypass Vulnerability Patched in Apache Solr
Apache Solr, a highly reliable and scalable search platform powering the search functionalities of some of the world’s largest internet sites, has been the target of two newly disclosed security vulne ... Read more

-
Help Net Security
87,000+ Fortinet devices still open to attack, are yours among them? (CVE-2024-23113)
Last week, CISA added CVE-2024-23113 – a critical vulnerability that allows unauthenticated remote code/command execution on unpatched Fortinet FortiGate firewalls – to its Known Exploited Vulnerabili ... Read more

-
The Register
Thousands of Fortinet instances vulnerable to actively exploited flaw
More than 86,000 Fortinet instances remain vulnerable to the critical flaw that attackers started exploiting last week, according to Shadowserver's data. The most recent count taken from Sunday put th ... Read more
The following table lists the changes that have been made to the
CVE-2024-23113 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 24, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-23113 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-23113 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-23113 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-23113 -
Modified Analysis by [email protected]
Nov. 29, 2024
Action Type Old Value New Value -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://fortiguard.com/psirt/FG-IR-24-029 -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Oct. 10, 2024
Action Type Old Value New Value Added Due Date 2024-10-30 Added Vulnerability Name Fortinet Multiple Products Format String Vulnerability Added Required Action Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable. Added Date Added 2024-10-09 -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
Initial Analysis by [email protected]
Feb. 22, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://fortiguard.com/psirt/FG-IR-24-029 No Types Assigned https://fortiguard.com/psirt/FG-IR-24-029 Vendor Advisory Added CPE Configuration OR *cpe:2.3:a:fortinet:fortiproxy:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.14 *cpe:2.3:a:fortinet:fortiproxy:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.8 *cpe:2.3:a:fortinet:fortiproxy:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (including) 7.4.2 *cpe:2.3:a:fortinet:fortiswitchmanager:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.3 *cpe:2.3:a:fortinet:fortiswitchmanager:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.3 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.13 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.6 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (including) 7.4.2 *cpe:2.3:o:fortinet:fortipam:*:*:*:*:*:*:*:* versions from (including) 1.0.0 up to (including) 1.0.3 *cpe:2.3:o:fortinet:fortipam:*:*:*:*:*:*:*:* versions from (including) 1.1.0 up to (including) 1.1.2 *cpe:2.3:o:fortinet:fortipam:1.2.0:*:*:*:*:*:*:* -
CVE Received by [email protected]
Feb. 15, 2024
Action Type Old Value New Value Added Description A use of externally-controlled format string in Fortinet FortiOS versions 7.4.0 through 7.4.2, 7.2.0 through 7.2.6, 7.0.0 through 7.0.13, FortiProxy versions 7.4.0 through 7.4.2, 7.2.0 through 7.2.8, 7.0.0 through 7.0.14, FortiPAM versions 1.2.0, 1.1.0 through 1.1.2, 1.0.0 through 1.0.3, FortiSwitchManager versions 7.2.0 through 7.2.3, 7.0.0 through 7.0.3 allows attacker to execute unauthorized code or commands via specially crafted packets. Added Reference Fortinet, Inc. https://fortiguard.com/psirt/FG-IR-24-029 [No types assigned] Added CWE Fortinet, Inc. CWE-134 Added CVSS V3.1 Fortinet, Inc. AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H