CVE-2024-0646
Kernel: ktls overwrites readonly memory pages when using function splice with a ktls socket as destination
Description
An out-of-bounds memory write flaw was found in the Linux kernel’s Transport Layer Security functionality in how a user calls a function splice with a ktls socket as the destination. This flaw allows a local user to crash or potentially escalate their privileges on the system.
INFO
Published Date :
Jan. 17, 2024, 4:15 p.m.
Last Modified :
Nov. 25, 2024, 10:44 a.m.
Remotely Exploit :
No
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-0646
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Update the affected kernel packages.
- Reboot the system after updating.
Public PoC/Exploit Available at Github
CVE-2024-0646 has a 4 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-0646.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-0646 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-0646
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
This was created for workshop 1 of PlatformCon - https://platformcon.com/sessions/hunting-compromised-software-dependencies-inside-kubernetes-workloads
Dockerfile
Local Vulnerabilities Check windows and linux
PowerShell Shell
This project was originally designed to compared CVSS scores with EPSS data via a simple command-line interface
Shell Python
Ini adalah repository kumpulan CVE v.5
allcve cve cvelist newcve
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-0646 vulnerability anywhere in the article.
-
Cybersecurity News
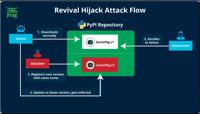
Revival Hijack: A New PyPI Hijacking Technique Threatens Thousands of Packages
The JFrog security research team has uncovered a novel PyPI package hijacking method known as “Revival Hijack,” which has put over 22,000 packages at risk of exploitation. Unlike traditional typosquat ... Read more

-
Cybersecurity News
Publicly Exposed GenAI Development Services Raise Serious Security Concerns
Access to the API without the need for any authentication | Image: Legit SecurityA new report released by Legit Security has raised significant concerns about the security posture of publicly accessib ... Read more

-
Cybersecurity News
Log4j Exploited Again: New Campaign Targets Vulnerable Systems with Crypto-Mining and Backdoors
Despite its discovery over two years ago, the Log4j vulnerability, known as Log4Shell (CVE-2021-44228), continues to pose a significant threat to global cybersecurity. A recent report from Datadog Sec ... Read more

-
Cybersecurity News
Gafgyt Botnet: Now Exploiting GPU Power in Cloud-Native Environments
Gafgyt attack flow | Image: Aqua NautilusResearchers at Aqua Nautilus have identified a new variant of the Gafgyt botnet that represents a significant evolution in malware targeting strategies. Origin ... Read more

-
Cybersecurity News
Google Pixel Phones Exposed: Millions at Risk Due to Pre-Installed App Vulnerability
Cybersecurity researchers at iVerify, in collaboration with Palantir Technologies and Trail of Bits, have uncovered a significant vulnerability in millions of Google Pixel devices worldwide. The flaw, ... Read more

-
Cybersecurity News
Linux Kernel Vulnerabilities Expose Systems to Privilege Escalation: Flaws Detailed and Exploit Code Released
Security researchers have disclosed the technical details and proof-of-concept (PoC) exploit codes for three vulnerabilities (CVE-2023-4206, CVE-2023-4207, and CVE-2023-4208) in the Linux kernel, impa ... Read more
The following table lists the changes that have been made to the
CVE-2024-0646 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by [email protected]
Nov. 25, 2024
Action Type Old Value New Value Added CWE CWE-787 Removed CWE CWE-1314 -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://access.redhat.com/errata/RHSA-2024:0723 Added Reference https://access.redhat.com/errata/RHSA-2024:0724 Added Reference https://access.redhat.com/errata/RHSA-2024:0725 Added Reference https://access.redhat.com/errata/RHSA-2024:0850 Added Reference https://access.redhat.com/errata/RHSA-2024:0851 Added Reference https://access.redhat.com/errata/RHSA-2024:0876 Added Reference https://access.redhat.com/errata/RHSA-2024:0881 Added Reference https://access.redhat.com/errata/RHSA-2024:0897 Added Reference https://access.redhat.com/errata/RHSA-2024:1248 Added Reference https://access.redhat.com/errata/RHSA-2024:1250 Added Reference https://access.redhat.com/errata/RHSA-2024:1251 Added Reference https://access.redhat.com/errata/RHSA-2024:1253 Added Reference https://access.redhat.com/errata/RHSA-2024:1268 Added Reference https://access.redhat.com/errata/RHSA-2024:1269 Added Reference https://access.redhat.com/errata/RHSA-2024:1278 Added Reference https://access.redhat.com/errata/RHSA-2024:1306 Added Reference https://access.redhat.com/errata/RHSA-2024:1367 Added Reference https://access.redhat.com/errata/RHSA-2024:1368 Added Reference https://access.redhat.com/errata/RHSA-2024:1377 Added Reference https://access.redhat.com/errata/RHSA-2024:1382 Added Reference https://access.redhat.com/errata/RHSA-2024:1404 Added Reference https://access.redhat.com/errata/RHSA-2024:2094 Added Reference https://access.redhat.com/security/cve/CVE-2024-0646 Added Reference https://bugzilla.redhat.com/show_bug.cgi?id=2253908 Added Reference https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=c5a595000e267 Added Reference https://lists.debian.org/debian-lts-announce/2024/06/msg00016.html -
CVE Modified by [email protected]
Oct. 16, 2024
Action Type Old Value New Value Added CWE Red Hat, Inc. CWE-1314 -
CVE Modified by [email protected]
Sep. 14, 2024
Action Type Old Value New Value Removed Reference Red Hat, Inc. https://lists.debian.org/debian-lts-announce/2024/06/msg00016.html -
Modified Analysis by [email protected]
Aug. 27, 2024
Action Type Old Value New Value Changed Reference Type https://access.redhat.com/errata/RHSA-2024:0723 No Types Assigned https://access.redhat.com/errata/RHSA-2024:0723 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:0724 No Types Assigned https://access.redhat.com/errata/RHSA-2024:0724 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:0725 No Types Assigned https://access.redhat.com/errata/RHSA-2024:0725 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:0850 No Types Assigned https://access.redhat.com/errata/RHSA-2024:0850 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:0851 No Types Assigned https://access.redhat.com/errata/RHSA-2024:0851 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:0876 No Types Assigned https://access.redhat.com/errata/RHSA-2024:0876 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:0881 No Types Assigned https://access.redhat.com/errata/RHSA-2024:0881 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:0897 No Types Assigned https://access.redhat.com/errata/RHSA-2024:0897 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1248 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1248 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1250 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1250 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1251 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1251 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1253 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1253 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1268 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1268 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1269 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1269 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1278 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1278 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1306 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1306 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1367 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1367 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1368 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1368 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1377 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1377 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1382 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1382 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:1404 No Types Assigned https://access.redhat.com/errata/RHSA-2024:1404 Third Party Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:2094 No Types Assigned https://access.redhat.com/errata/RHSA-2024:2094 Third Party Advisory Changed Reference Type https://lists.debian.org/debian-lts-announce/2024/06/msg00016.html No Types Assigned https://lists.debian.org/debian-lts-announce/2024/06/msg00016.html Issue Tracking, Third Party Advisory Changed CPE Configuration OR *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions up to (excluding) 6.7 *cpe:2.3:o:linux:linux_kernel:6.7:rc1:*:*:*:*:*:* *cpe:2.3:o:linux:linux_kernel:6.7:rc2:*:*:*:*:*:* *cpe:2.3:o:linux:linux_kernel:6.7:rc3:*:*:*:*:*:* *cpe:2.3:o:linux:linux_kernel:6.7:rc4:*:*:*:*:*:* OR *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 4.20 up to (excluding) 5.4.267 *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 5.5 up to (excluding) 5.10.208 *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 5.11 up to (excluding) 5.15.147 *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 5.16 up to (excluding) 6.1.69 *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 6.2 up to (excluding) 6.6.7 *cpe:2.3:o:linux:linux_kernel:6.7:rc1:*:*:*:*:*:* *cpe:2.3:o:linux:linux_kernel:6.7:rc2:*:*:*:*:*:* *cpe:2.3:o:linux:linux_kernel:6.7:rc3:*:*:*:*:*:* *cpe:2.3:o:linux:linux_kernel:6.7:rc4:*:*:*:*:*:* -
CVE Modified by [email protected]
Jul. 08, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:2094 [No types assigned] -
CVE Modified by [email protected]
Jun. 25, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://lists.debian.org/debian-lts-announce/2024/06/msg00016.html [No types assigned] -
CVE Modified by [email protected]
May. 23, 2024
Action Type Old Value New Value -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CVE Modified by [email protected]
Mar. 19, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1404 [No types assigned] -
CVE Modified by [email protected]
Mar. 19, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1377 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1382 [No types assigned] -
CVE Modified by [email protected]
Mar. 19, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1367 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1368 [No types assigned] -
CVE Modified by [email protected]
Mar. 13, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1306 [No types assigned] -
CVE Modified by [email protected]
Mar. 12, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1278 [No types assigned] -
CVE Modified by [email protected]
Mar. 12, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1268 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1269 [No types assigned] -
CVE Modified by [email protected]
Mar. 12, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1248 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1250 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1251 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:1253 [No types assigned] -
CVE Modified by [email protected]
Feb. 20, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:0881 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:0897 [No types assigned] -
CVE Modified by [email protected]
Feb. 20, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:0876 [No types assigned] -
CVE Modified by [email protected]
Feb. 15, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:0850 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:0851 [No types assigned] -
CVE Modified by [email protected]
Feb. 07, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:0723 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:0724 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:0725 [No types assigned] -
Initial Analysis by [email protected]
Jan. 24, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://access.redhat.com/security/cve/CVE-2024-0646 No Types Assigned https://access.redhat.com/security/cve/CVE-2024-0646 Third Party Advisory Changed Reference Type https://bugzilla.redhat.com/show_bug.cgi?id=2253908 No Types Assigned https://bugzilla.redhat.com/show_bug.cgi?id=2253908 Issue Tracking, Patch Changed Reference Type https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=c5a595000e267 No Types Assigned https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=c5a595000e267 Patch Added CWE NIST CWE-787 Added CPE Configuration OR *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions up to (excluding) 6.7 *cpe:2.3:o:linux:linux_kernel:6.7:rc1:*:*:*:*:*:* *cpe:2.3:o:linux:linux_kernel:6.7:rc2:*:*:*:*:*:* *cpe:2.3:o:linux:linux_kernel:6.7:rc3:*:*:*:*:*:* *cpe:2.3:o:linux:linux_kernel:6.7:rc4:*:*:*:*:*:* Added CPE Configuration OR *cpe:2.3:o:redhat:enterprise_linux:8.0:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux:9.0:*:*:*:*:*:*:* -
CVE Received by [email protected]
Jan. 17, 2024
Action Type Old Value New Value Added Description An out-of-bounds memory write flaw was found in the Linux kernel’s Transport Layer Security functionality in how a user calls a function splice with a ktls socket as the destination. This flaw allows a local user to crash or potentially escalate their privileges on the system. Added Reference Red Hat, Inc. https://access.redhat.com/security/cve/CVE-2024-0646 [No types assigned] Added Reference Red Hat, Inc. https://bugzilla.redhat.com/show_bug.cgi?id=2253908 [No types assigned] Added Reference Red Hat, Inc. https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=c5a595000e267 [No types assigned] Added CVSS V3.1 Red Hat, Inc. AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H