CVE-2024-6386
WPML Multilingual CMS <= 4.6.12 - Authenticated (Contributor+) Remote Code Execution via Twig Server-Side Template Injection
Description
The WPML plugin for WordPress is vulnerable to Remote Code Execution in all versions up to, and including, 4.6.12 via Twig Server-Side Template Injection. This is due to missing input validation and sanitization on the render function. This makes it possible for authenticated attackers, with Contributor-level access and above, to execute code on the server.
INFO
Published Date :
Aug. 21, 2024, 9:15 p.m.
Last Modified :
April 8, 2026, 7:22 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
Public PoC/Exploit Available at Github
CVE-2024-6386 has a 9 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-6386.
| URL | Resource |
|---|---|
| https://sec.stealthcopter.com/wpml-rce-via-twig-ssti/ | Exploit Third Party Advisory |
| https://wpml.org/ | Product |
| https://www.wordfence.com/threat-intel/vulnerabilities/id/f7fc91cc-e529-4362-8269-bf7ee0766e1e?source=cve | Third Party Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-6386 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-6386
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
None
A collection of Vulnerability Research and Reverse Engineering writeups.
Extra plugins for SSTImap
Python
Research and PoC for CVE-2024-6386
Python
CVE-2024-6386 - Wordpress WPML (WordPress Multilingual Plugin) ≤ 4.6.12. RCE Exploit 0Day (300K Sites Vulnerability) -- Telegram: @bl4ckhatx
0day code cve cve-2024 exploit hack injection rce remote shell tool unauth vuln vulnaribility wordpress wp
CVE-2024-6386 - Wordpress WPML (WordPress Multilingual Plugin) ≤ 4.6.12. RCE Exploit 0Day (300K Sites Vulnerability) -- Telegram: @bl4ckhatx
hack poc rce wordpress wpml cve-2024-6386
Automatic SSTI detection tool with interactive interface
information-security penetration-testing penetration-testing-tools pentest pentest-tool pentesting pentesting-tools rce ssti python
Python
Ostorlab KEV: One-command to detect most remotely known exploitable vulnerabilities. Sourced from CISA KEV, Google's Tsunami, Ostorlab's Asteroid and Bug Bounty programs.
cisa-kev vulnerability 0day cisa exploits
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-6386 vulnerability anywhere in the article.

-
Cybersecurity News
CVSS 9.8 Vulnerabilities Expose Aruba Access Points to RCE: HPE Urges Immediate Action
The Hewlett Packard Enterprise (HPE) Product Security Response Team has issued a critical advisory concerning multiple command injection vulnerabilities (CVE-2024-42505, CVE-2024-42506, CVE-2024-42507 ... Read more

-
Cybersecurity News
30 Exploitable Flaws: Alarming Study on Home Router Defaults
A study titled “Exposed by Default: A Security Analysis of Home Router Default Settings” has shed light on the pervasive vulnerabilities present in home routers, highlighting significant risks associa ... Read more

-
Cybersecurity News
CVE-2024-47062 (CVSS 9.4): Flaws Discovered in Navidrome Music Server Expose Sensitive Data
In a newly published security advisory, several critical vulnerabilities have been identified in Navidrome, a popular open-source music streaming server. These flaws, disclosed under CVE-2024-47062 wi ... Read more

-
Cybersecurity News
Unmasking “Marko Polo”: The Infostealer Gang Targeting Thousands
Marko Polo infection chain (Source: Recorded Future)Researchers at Recorded Future have uncovered a large-scale cyberattack affecting tens of thousands of devices worldwide. It was later revealed that ... Read more

-
Cybersecurity News
CISA Flags Two Actively Exploited Vulnerabilities: Critical Threats to Windows and WhatsUp Gold
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning, adding two actively exploited security flaws to its Known Exploited Vulnerabilities (KEV) catalog, urging immedia ... Read more

-
Cybersecurity News
Exploit Kits, Cryptominers, Proxyjackers: The New Face of Selenium Grid Abuse
Researchers at Cado Security Labs have uncovered two malicious campaigns that exploit misconfigured instances of Selenium Grid. Once a trusted tool for browser automation and testing, Selenium Grid ha ... Read more
-
Cybersecurity News
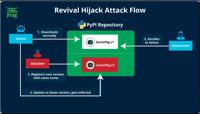
Revival Hijack: A New PyPI Hijacking Technique Threatens Thousands of Packages
The JFrog security research team has uncovered a novel PyPI package hijacking method known as “Revival Hijack,” which has put over 22,000 packages at risk of exploitation. Unlike traditional typosquat ... Read more

-
Cybersecurity News
Publicly Exposed GenAI Development Services Raise Serious Security Concerns
Access to the API without the need for any authentication | Image: Legit SecurityA new report released by Legit Security has raised significant concerns about the security posture of publicly accessib ... Read more

-
The Cyber Express
Critical WPML Plugin Flaw Exposes Millions of WordPress Sites to Remote Code Execution
A critical vulnerability has been discovered in the WPML (WordPress Multilingual) plugin, exposing millions of WordPress websites to potential Remote Code Execution (RCE) attacks. This WPML Plugin Fla ... Read more

-
TheCyberThrone
WordPress WPML Plugin Critical Vulnerability CVE-2024-6386
Researchers have uncovered a critical vulnerability in WPML multilingual CMS Plugin for WordPress that leads to a Remote Code Execution, which potentially allows the compromise of impacted websites.Th ... Read more

-
The Hacker News
Critical WPML Plugin Flaw Exposes WordPress Sites to Remote Code Execution
WordPress Security / Website Protection A critical security flaw has been disclosed in the WPML WordPress multilingual plugin that could allow authenticated users to execute arbitrary code remotely un ... Read more

-
TheCyberThrone
CISA adds Apache OFBiz Vulnerability CVE-2024-38856 to KEV Catalog
The U.S. CISA adds Apache OFBiz vulnerability to its KEV catalog following the mass exploitationCVE-2024-38856 : Apache OFBiz Incorrect Authorization Vulnerability: Apache OFBiz contains an incorrect ... Read more

-
security.nl
Kritiek RCE-lek in WPML WordPressplug-in met één miljoen installaties
Een kritieke kwetsbaarheid in WPML, een plug-in voor WordPress-sites met meer dan één miljoen installaties, maakt het mogelijk om kwetsbare websites op afstand over te nemen. De impact van de kwetsbaa ... Read more

-
Cybersecurity News
CVE-2024-6386 (CVSS 9.9) in WPML Plugin Exposes Millions of WordPress Sites to RCE Attacks
A severe security flaw (CVE-2024-6386, CVSS 9.9) has been discovered in the widely-used WPML plugin for WordPress, potentially exposing over one million websites to the risk of complete takeover. The ... Read more

-
Cybersecurity News
Log4j Exploited Again: New Campaign Targets Vulnerable Systems with Crypto-Mining and Backdoors
Despite its discovery over two years ago, the Log4j vulnerability, known as Log4Shell (CVE-2021-44228), continues to pose a significant threat to global cybersecurity. A recent report from Datadog Sec ... Read more
The following table lists the changes that have been made to the
CVE-2024-6386 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by [email protected]
Apr. 08, 2026
Action Type Old Value New Value Changed Description The WPML plugin for WordPress is vulnerable to Remote Code Execution in all versions up to, and including, 4.6.12 via the Twig Server-Side Template Injection. This is due to missing input validation and sanitization on the render function. This makes it possible for authenticated attackers, with Contributor-level access and above, to execute code on the server. The WPML plugin for WordPress is vulnerable to Remote Code Execution in all versions up to, and including, 4.6.12 via Twig Server-Side Template Injection. This is due to missing input validation and sanitization on the render function. This makes it possible for authenticated attackers, with Contributor-level access and above, to execute code on the server. -
Initial Analysis by [email protected]
Sep. 27, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://sec.stealthcopter.com/wpml-rce-via-twig-ssti/ No Types Assigned https://sec.stealthcopter.com/wpml-rce-via-twig-ssti/ Exploit, Third Party Advisory Changed Reference Type https://wpml.org/ No Types Assigned https://wpml.org/ Product Changed Reference Type https://www.wordfence.com/threat-intel/vulnerabilities/id/f7fc91cc-e529-4362-8269-bf7ee0766e1e?source=cve No Types Assigned https://www.wordfence.com/threat-intel/vulnerabilities/id/f7fc91cc-e529-4362-8269-bf7ee0766e1e?source=cve Third Party Advisory Added CWE NIST CWE-94 Added CPE Configuration OR *cpe:2.3:a:wpml:wpml:*:*:*:*:*:wordpress:*:* versions up to (excluding) 4.6.13 -
CVE Received by [email protected]
Aug. 21, 2024
Action Type Old Value New Value Added Description The WPML plugin for WordPress is vulnerable to Remote Code Execution in all versions up to, and including, 4.6.12 via the Twig Server-Side Template Injection. This is due to missing input validation and sanitization on the render function. This makes it possible for authenticated attackers, with Contributor-level access and above, to execute code on the server. Added Reference Wordfence https://www.wordfence.com/threat-intel/vulnerabilities/id/f7fc91cc-e529-4362-8269-bf7ee0766e1e?source=cve [No types assigned] Added Reference Wordfence https://wpml.org/ [No types assigned] Added Reference Wordfence https://sec.stealthcopter.com/wpml-rce-via-twig-ssti/ [No types assigned] Added CWE Wordfence CWE-1336 Added CVSS V3.1 Wordfence AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H