CVE-2024-42019
Veeam Reporter Service NTLM Hash Disclosure
Description
A vulnerability that allows an attacker to access the NTLM hash of the Veeam Reporter Service service account. This attack requires user interaction and data collected from Veeam Backup & Replication.
INFO
Published Date :
Sept. 7, 2024, 5:15 p.m.
Last Modified :
May 1, 2025, 6:19 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.0 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-42019.
| URL | Resource |
|---|---|
| https://www.veeam.com/kb4649 | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-42019 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-42019
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-42019 vulnerability anywhere in the article.
-
Cybersecurity News
CVE-2024-8698: Keycloak Vulnerability Puts SAML Authentication at Risk
Image: KeycloakIn a concerning development for organizations relying on Keycloak for secure identity and access management, a high-severity vulnerability has been discovered in its SAML signature vali ... Read more

-
Cybersecurity News
New Zero-Day Emerges After Microsoft Patch Tuesday: CVE-2024-43461 Targets Windows MSHTML
IE and a promote window dialog appear when the victim double-clicks on the .url file | Image: Check PointIn an unexpected turn of events, Microsoft has revised its September 2024 Patch Tuesday securit ... Read more
-
Cybersecurity News
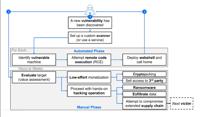
Medusa Exploits Fortinet Flaw (CVE-2023-48788) for Stealthy Ransomware Attacks
A recent report from Bitdefender highlights how Medusa has not only continued its relentless attacks but has also established a unique online presence on both the dark web and the surface web, making ... Read more

-
Cybersecurity News
Hackers target Apache OFBiz RCE flaw CVE-2024-45195 after PoC exploit released
Image: Rapid7According to a report from Imperva, over 25,000 malicious requests targeting 4,000 unique sites have been detected since the CVE-2024-45195 vulnerability in Apache OFBiz was disclosed. Th ... Read more

-
Cybersecurity News
CVE-2024-43491 (CVSS 9.8): Critical Windows 0-Day Flaw Uncovered, Urgent Patching Required
Microsoft has disclosed a critical zero-day vulnerability in its Windows operating system, identified as CVE-2024-43491. The vulnerability, with a severity score of 9.8 (out of 10), resides within the ... Read more

-
The Cyber Express
Veeam Security Bulletin Fixes Critical Vulnerabilities for Backup & Replication, Veeam ONE and More
Veeam has published a new Security Bulletin addressing multiple critical vulnerabilities across its suite of products. The Veeam security bulletin, identified as KB ID: 4649, includes updates on Veeam ... Read more

-
The Hacker News
Veeam Releases Security Updates to Fix 18 Flaws, Including 5 Critical Issues
Threat Prevention / Software Security Veeam has shipped security updates to address a total of 18 security flaws impacting its software products, including five critical vulnerabilities that could res ... Read more

-
BleepingComputer
Veeam warns of critical RCE flaw in Backup & Replication software
Veeam has released security updates for several of its products as part of a single September 2024 security bulletin that addresses 18 high and critical severity flaws in Veeam Backup & Replication, S ... Read more
The following table lists the changes that have been made to the
CVE-2024-42019 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
May. 01, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H Added CPE Configuration OR *cpe:2.3:a:veeam:one:*:*:*:*:*:*:*:* versions up to (excluding) 12.2.0.4093 Added Reference Type HackerOne: https://www.veeam.com/kb4649 Types: Vendor Advisory -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Sep. 09, 2024
Action Type Old Value New Value Added CWE CISA-ADP CWE-200 -
CVE Received by [email protected]
Sep. 07, 2024
Action Type Old Value New Value Added Description A vulnerability that allows an attacker to access the NTLM hash of the Veeam Reporter Service service account. This attack requires user interaction and data collected from Veeam Backup & Replication. Added Reference HackerOne https://www.veeam.com/kb4649 [No types assigned] Added CVSS V3 HackerOne AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:H/A:H