CVE-2024-52067
Apache NiFi: Potential Insertion of Sensitive Parameter Values in Debug Log
Description
Apache NiFi 1.16.0 through 1.28.0 and 2.0.0-M1 through 2.0.0-M4 include optional debug logging of Parameter Context values during the flow synchronization process. An authorized administrator with access to change logging levels could enable debug logging for framework flow synchronization, causing the application to write Parameter names and values to the application log. Parameter Context values may contain sensitive information depending on application flow configuration. Deployments of Apache NiFi with the default Logback configuration do not log Parameter Context values. Upgrading to Apache NiFi 2.0.0 or 1.28.1 is the recommendation mitigation, eliminating Parameter value logging from the flow synchronization process regardless of the Logback configuration.
INFO
Published Date :
Nov. 21, 2024, 11:15 a.m.
Last Modified :
Feb. 11, 2025, 4:26 p.m.
Remotely Exploit :
No
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | MEDIUM | [email protected] | ||||
| CVSS 4.0 | MEDIUM | [email protected] |
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-52067.
| URL | Resource |
|---|---|
| https://lists.apache.org/thread/9rz5rwn2zc7pfjq7ppqldqlc067tlcwd | Mailing List |
| http://www.openwall.com/lists/oss-security/2024/11/20/2 | Mailing List |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-52067 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-52067
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-52067 vulnerability anywhere in the article.

-
Daily CyberSecurity
Apache NiFi’s Data Leak: How a High-Severity Deserialization Flaw Puts Your Asana Workflows at Risk
The Apache Software Foundation has issued a security advisory for Apache NiFi, the powerful data processing engine used by thousands of enterprises to automate data flow between systems. A high-severi ... Read more

-
Cybersecurity News
CVE-2024-56512: Apache NiFi Vulnerability Exposes Sensitive Data to Unauthorized Users
A newly discovered vulnerability in Apache NiFi, a widely used data processing and distribution system, could allow unauthorized access to sensitive information. The vulnerability, tracked as CVE-2024 ... Read more

-
Cybersecurity News
336,000 Prometheus Servers at Risk: Urgent Security Alert
In a recent investigation, Aqua Nautilus uncovered alarming security vulnerabilities within the Prometheus ecosystem. Their research highlights critical flaws spanning information disclosure, denial-o ... Read more

-
Cybersecurity News
Abusing Microsoft’s UI Automation Framework: The New Evasion Technique Bypassing EDR
Akamai security researcher Tomer Peled has unveiled a novel attack technique exploiting Microsoft’s legacy UI Automation framework, a tool originally designed to enhance computer accessibility. The fi ... Read more

-
Cybersecurity News
Modular Java Backdoor Emerges in Cleo Exploitation Campaign (CVE-2024-50623)
Rapid7 Labs and its Managed Detection and Response (MDR) team uncovered a sophisticated modular Java-based Remote Access Trojan (RAT) deployed in a multi-stage attack targeting Cleo file transfer soft ... Read more

-
Cybersecurity News
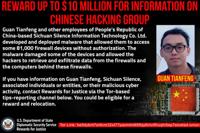
$5 Million Reward Offered After Indictment of North Korean Cyber Operatives
A federal court in St. Louis, Missouri, has indicted 14 nationals of the Democratic People’s Republic of Korea (DPRK) for a series of long-running conspiracies involving sanctions violations, wire fra ... Read more
-
Cybersecurity News
CVE-2020-12271 Exploited: FBI Seeks Chinese Hacker Behind 81,000 Device Breach
The US Department of Justice announced the unsealing of an indictment against Guan Tianfeng, a Chinese national associated with Sichuan Silence Information Technology Co. Ltd., for his alleged role in ... Read more

-
Cybersecurity News
Ivanti Connect Secure and Policy Secure Updates Address Critical Vulnerabilities
Ivanti, a leader in unified endpoint and enterprise service management, has issued patches for several high and critical vulnerabilities affecting its Connect Secure and Policy Secure solutions. These ... Read more

-
Cybersecurity News
CVE-2024-52335 (CVSS 9.8): Siemens Healthineers Addresses Critical Flaw in Medical Imaging Software
Siemens Healthineers has released a critical security update to address an unauthenticated SQL injection vulnerability in its syngo.plaza VB30E medical imaging software. The vulnerability, identified ... Read more

-
Cybersecurity News
Google Chrome Patches High-Severity Vulnerabilities – CVE-2024-12381 & CVE-2024-12382
Google has announced its Chrome browser’s latest stable channel update, addressing several security vulnerabilities, including two classified as “High” severity. The update, rolling out progressively ... Read more

-
Cybersecurity News
Beware of Celestial Stealer: New MaaS Targets Browsers and Crypto Wallets
A new report from Trellix Advanced Research Center has exposed the inner workings of Celestial Stealer, a sophisticated Malware-as-a-Service (MaaS) platform targeting developers, gamers, and cryptocur ... Read more

-
Cybersecurity News
Google Chrome Addresses High-Severity Flaw in V8 JavaScript Engine (CVE-2024-12053)
Google has released a security update for its Chrome web browser to mitigate a high-severity “type confusion” vulnerability (CVE-2024-12053) residing within the V8 JavaScript engine. This vulnerabilit ... Read more
-
Cybersecurity News
XorBot Botnet Resurfaces with Advanced Evasion and Exploits, Threatens IoT Devices
NSFOCUS has identified a resurgence of the XorBot botnet, a potent threat to Internet of Things (IoT) devices worldwide. First observed in late 2023, XorBot has evolved significantly, introducing adva ... Read more
The following table lists the changes that have been made to the
CVE-2024-52067 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Feb. 11, 2025
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:N/A:N Added CPE Configuration OR *cpe:2.3:a:apache:nifi:*:*:*:*:*:*:*:* versions from (including) 1.16.0 up to (excluding) 1.28.1 *cpe:2.3:a:apache:nifi:2.0.0:milestone1:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone1-rc1:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone1-rc2:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone1-rc3:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone1-rc4:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone1-rc5:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone1-rc6:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone2:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone2-rc1:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone2-rc2:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone2-rc3:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone2-rc4:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone3:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone3-rc1:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone4:*:*:*:*:*:* *cpe:2.3:a:apache:nifi:2.0.0:milestone4-rc1:*:*:*:*:*:* Changed Reference Type http://www.openwall.com/lists/oss-security/2024/11/20/2 No Types Assigned http://www.openwall.com/lists/oss-security/2024/11/20/2 Mailing List Changed Reference Type https://lists.apache.org/thread/9rz5rwn2zc7pfjq7ppqldqlc067tlcwd No Types Assigned https://lists.apache.org/thread/9rz5rwn2zc7pfjq7ppqldqlc067tlcwd Mailing List -
New CVE Received by [email protected]
Nov. 21, 2024
Action Type Old Value New Value Added Description Apache NiFi 1.16.0 through 1.28.0 and 2.0.0-M1 through 2.0.0-M4 include optional debug logging of Parameter Context values during the flow synchronization process. An authorized administrator with access to change logging levels could enable debug logging for framework flow synchronization, causing the application to write Parameter names and values to the application log. Parameter Context values may contain sensitive information depending on application flow configuration. Deployments of Apache NiFi with the default Logback configuration do not log Parameter Context values. Upgrading to Apache NiFi 2.0.0 or 1.28.1 is the recommendation mitigation, eliminating Parameter value logging from the flow synchronization process regardless of the Logback configuration. Added CVSS V4.0 AV:L/AC:L/AT:P/PR:H/UI:N/VC:H/VI:L/VA:N/SC:H/SI:L/SA:N/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:X/AU:Y/R:U/V:D/RE:L/U:Green Added CWE CWE-532 Added Reference https://lists.apache.org/thread/9rz5rwn2zc7pfjq7ppqldqlc067tlcwd -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference http://www.openwall.com/lists/oss-security/2024/11/20/2