CVE-2024-5082
Nexus Repository 2 - Remote Code Execution
Description
A Remote Code Execution vulnerability has been discovered in Sonatype Nexus Repository 2. This issue affects Nexus Repository 2 OSS/Pro versions up to and including 2.15.1.
INFO
Published Date :
Nov. 14, 2024, 3:15 a.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
103e4ec9-0a87-450b-af77-479448ddef11
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 4.0 | HIGH | 103e4ec9-0a87-450b-af77-479448ddef11 |
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-5082.
| URL | Resource |
|---|---|
| https://support.sonatype.com/hc/en-us/articles/30694125380755 |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-5082 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-5082
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-5082 vulnerability anywhere in the article.

-
Daily CyberSecurity
Lazarus Group’s Covert Supply Chain Attack: North Korean APT Poisons Open Source to Steal Developer Secrets
Image: Sonatype In a recently expose, Sonatype reveals a covert cyberespionage campaign orchestrated by the North Korea-linked Lazarus Group, targeting developers through poisoned open source packages ... Read more

-
Cybersecurity News
336,000 Prometheus Servers at Risk: Urgent Security Alert
In a recent investigation, Aqua Nautilus uncovered alarming security vulnerabilities within the Prometheus ecosystem. Their research highlights critical flaws spanning information disclosure, denial-o ... Read more

-
Cybersecurity News
Abusing Microsoft’s UI Automation Framework: The New Evasion Technique Bypassing EDR
Akamai security researcher Tomer Peled has unveiled a novel attack technique exploiting Microsoft’s legacy UI Automation framework, a tool originally designed to enhance computer accessibility. The fi ... Read more

-
Cybersecurity News
Modular Java Backdoor Emerges in Cleo Exploitation Campaign (CVE-2024-50623)
Rapid7 Labs and its Managed Detection and Response (MDR) team uncovered a sophisticated modular Java-based Remote Access Trojan (RAT) deployed in a multi-stage attack targeting Cleo file transfer soft ... Read more

-
Cybersecurity News
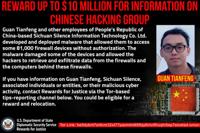
$5 Million Reward Offered After Indictment of North Korean Cyber Operatives
A federal court in St. Louis, Missouri, has indicted 14 nationals of the Democratic People’s Republic of Korea (DPRK) for a series of long-running conspiracies involving sanctions violations, wire fra ... Read more
-
Cybersecurity News
CVE-2020-12271 Exploited: FBI Seeks Chinese Hacker Behind 81,000 Device Breach
The US Department of Justice announced the unsealing of an indictment against Guan Tianfeng, a Chinese national associated with Sichuan Silence Information Technology Co. Ltd., for his alleged role in ... Read more

-
Cybersecurity News
Ivanti Connect Secure and Policy Secure Updates Address Critical Vulnerabilities
Ivanti, a leader in unified endpoint and enterprise service management, has issued patches for several high and critical vulnerabilities affecting its Connect Secure and Policy Secure solutions. These ... Read more

-
Cybersecurity News
Google Chrome Patches High-Severity Vulnerabilities – CVE-2024-12381 & CVE-2024-12382
Google has announced its Chrome browser’s latest stable channel update, addressing several security vulnerabilities, including two classified as “High” severity. The update, rolling out progressively ... Read more
-
Cybersecurity News
XorBot Botnet Resurfaces with Advanced Evasion and Exploits, Threatens IoT Devices
NSFOCUS has identified a resurgence of the XorBot botnet, a potent threat to Internet of Things (IoT) devices worldwide. First observed in late 2023, XorBot has evolved significantly, introducing adva ... Read more

-
Cybersecurity News
NVIDIA Base Command Manager Update Patches CVE-2024-0138 (CVSS 9.8)
NVIDIA has issued a critical security update for its Base Command Manager software, addressing a vulnerability that could open systems to a range of serious attacks. The flaw, tracked as CVE-2024-0138 ... Read more

-
Cybersecurity News
Sonatype Nexus Repository 2 Hit By RCE (CVE-2024-5082) and XSS (CVE-2024-5083) Flaws
Sonatype has issued two security advisories for its Nexus Repository Manager 2.x, a popular repository manager used by organizations worldwide to store and distribute software artifacts, warning users ... Read more
The following table lists the changes that have been made to the
CVE-2024-5082 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Nov. 21, 2024
Action Type Old Value New Value Removed CVSS V3.1 AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Nov. 14, 2024
Action Type Old Value New Value Added CVSS V3.1 CISA-ADP AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N -
CVE Received by 103e4ec9-0a87-450b-af77-479448ddef11
Nov. 14, 2024
Action Type Old Value New Value Added Description A Remote Code Execution vulnerability has been discovered in Sonatype Nexus Repository 2. This issue affects Nexus Repository 2 OSS/Pro versions up to and including 2.15.1. Added Reference Sonatype https://support.sonatype.com/hc/en-us/articles/30694125380755 [No types assigned] Added CWE Sonatype CWE-94 Added CVSS V4.0 Sonatype CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:H/VI:L/VA:N/SC:N/SI:L/SA:N/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:X/AU:X/R:X/V:X/RE:X/U:X