CVE-2024-8105
Insecure Platform Key (PK) used in UEFI system firmware signature
Description
A vulnerability related to the use an insecure Platform Key (PK) has been discovered. An attacker with the compromised PK private key can create malicious UEFI software that is signed with a trusted key that has been compromised.
INFO
Published Date :
Aug. 26, 2024, 8:15 p.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
No
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-8105
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
No affected product recoded yet
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | MEDIUM | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-8105.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-8105 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-8105
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-8105 vulnerability anywhere in the article.

-
The Hacker News
THN Cybersecurity Recap: Last Week's Top Threats and Trends (September 23-29)
Cybersecurity / Weekly Recap Hold onto your hats, folks, because the cybersecurity world is anything but quiet! Last week, we dodged a bullet when we discovered vulnerabilities in CUPS that could've o ... Read more

-
Cybersecurity News
Critical XSS Flaw Discovered in Filament: CVE-2024-47186 Requires Urgent Update for Laravel Developers
The Filament project, a popular collection of full-stack components for accelerated Laravel development, has issued a critical security advisory for CVE-2024-47186. This Cross-Site Scripting (XSS) vul ... Read more

-
Cybersecurity News
RFC 9620: A Call for Human Rights in Internet Protocols
The Internet Research Task Force (IRTF) has released a new document, RFC 9620, aimed at drawing the attention of protocol and architecture developers to critical human rights issues.The document is in ... Read more

-
BleepingComputer
PKfail Secure Boot bypass remains a significant risk two months later
Roughly nine percent of tested firmware images use non-production cryptographic keys that are publicly known or leaked in data breaches, leaving many Secure Boot devices vulnerable to UEFI bootkit mal ... Read more

-
Ars Technica
Secure Boot-neutering PKfail debacle is more prevalent than anyone knew
THIS IS NOT A TEST — Keys were marked "DO NOT TRUST." More devices than previously known used them anyway. Getty Images A supply chain failure that compromises Secure Boot protections on computing ... Read more
-
Cybersecurity News
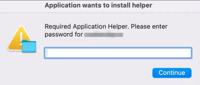
Don’t Fall for the Bait: Poseidon Stealer Masquerades as Sopha AI
Dialog box prompting the user to enter the password | Image: TRUIn a new wave of cyberattacks, macOS users are being targeted by the Poseidon Stealer malware, disguised as an installer for the highly ... Read more

-
Cybersecurity News
Veeam Backup & Replication Faces RCE Flaw– CVE-2024-40711 (CVSS 9.8) Allows Full System Takeover
A series of critical vulnerabilities have been uncovered in Veeam Backup & Replication, potentially exposing organizations to unauthorized access, remote code execution, and data breaches. The most se ... Read more

-
Cybersecurity News
CISA Issues Alert: Three Actively Exploited Vulnerabilities Demand Immediate Attention
The Cybersecurity and Infrastructure Security Agency (CISA) has added three critical vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, highlighting their active exploitation in the ... Read more

-
Cybersecurity News
CVE-2024-8105: An UEFI Flaw Putting Millions of Devices at Risk
Image: Binarly REsearch TeamA significant vulnerability, CVE-2024-8105, dubbed PKfail, has surfaced within the UEFI ecosystem. With a CVSS score of 8.2, this flaw exposes critical UEFI security mechan ... Read more
The following table lists the changes that have been made to the
CVE-2024-8105 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://www.kb.cert.org/vuls/id/455367 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Sep. 09, 2024
Action Type Old Value New Value Added CVSS V3.1 CISA-ADP AV:L/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H -
CVE Modified by [email protected]
Aug. 30, 2024
Action Type Old Value New Value Added Reference CERT/CC https://www.binarly.io/advisories/brly-2024-005 [No types assigned] Added Reference CERT/CC https://kb.cert.org/vuls/id/455367 [No types assigned] Added Reference CERT/CC https://www.gigabyte.com/us/Support/Security/2205 [No types assigned] -
CVE Received by [email protected]
Aug. 26, 2024
Action Type Old Value New Value Added Description A vulnerability related to the use an insecure Platform Key (PK) has been discovered. An attacker with the compromised PK private key can create malicious UEFI software that is signed with a trusted key that has been compromised. Added Reference CERT/CC https://uefi.org/specs/UEFI/2.9_A/32_Secure_Boot_and_Driver_Signing.html [No types assigned] Added Reference CERT/CC https://github.com/binarly-io/Vulnerability-REsearch/blob/main/PKfail/BRLY-2024-005.md [No types assigned] Added Reference CERT/CC https://www.supermicro.com/en/support/security_PKFAIL_Jul_2024 [No types assigned] Added Reference CERT/CC https://www.intel.com/content/www/us/en/security-center/announcement/intel-security-announcement-2024-07-25-001.html [No types assigned] Added Reference CERT/CC https://security.ts.fujitsu.com/ProductSecurity/content/Fujitsu-PSIRT-FJ-ISS-2024-072412-Security-Notice.pdf [No types assigned]