CVE-2024-30051
Microsoft DWM Core Library Privilege Escalation Vulnerability - [Actively Exploited]
Description
Windows DWM Core Library Elevation of Privilege Vulnerability
INFO
Published Date :
May 14, 2024, 5:17 p.m.
Last Modified :
Oct. 28, 2025, 2:23 p.m.
Remotely Exploit :
No
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Microsoft DWM Core Library contains a privilege escalation vulnerability that allows an attacker to gain SYSTEM privileges.
Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
Known Detected Feb 26, 2026
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-30051; https://nvd.nist.gov/vuln/detail/CVE-2024-30051
Affected Products
The following products are affected by CVE-2024-30051
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Apply the latest security updates.
- Reboot the system if prompted.
Public PoC/Exploit Available at Github
CVE-2024-30051 has a 10 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-30051.
| URL | Resource |
|---|---|
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-30051 | Patch Vendor Advisory |
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-30051 | Patch Vendor Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-30051 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-30051 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-30051
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
Master's Thesis research on CVE-2024-30051 (Windows DWM Heap Overflow). Features a high-reliability exploit with automated heap spray optimization, real-time logging, and empirical success-rate analysis. Portfolio piece demonstrating advanced Windows binary exploitation, heap layout manipulation, and LPE via Desktop Window Manager.
C++ C Batchfile
A research-focused archive of publicly disclosed Windows zero-day vulnerabilities. This project summarizes CVEs, disclosure timelines, vendor advisories, and defensive mitigations. ⚠️ No exploit code included — educational and defensive use only.
cve cybersecurity infosec security-research threat-intelligence vulnerabilities windows zero-day
HTML
None
None
C++
Here I store my proof of concepts
CMake C++ HTML C
An automated repo to track Nuclei template scanning capabilities against the CISA KEV.
cisa-kev nuclei scanning vulnerabilities cisa
Makefile Python Shell
Get quick summary of vulnerability stats and updates for Patch Tuesday.
security python3
Python
TOP All bugbounty pentesting CVE-2023- POC Exp RCE example payload Things
bugbounty cve exp exploit payload poc rce vulnerability
Shell
Collection of Windows Privilege Escalation (Analyse/PoC/Exploit)
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-30051 vulnerability anywhere in the article.

-
Daily CyberSecurity
Patch Panic: Microsoft Fixes 6 Active Zero-Days in Feb 2026 Update
Microsoft has released its security update for February 2026, addressing 61 vulnerabilities across its ecosystem. But the headline isn’t the volume of patches—it’s the urgency. The tech giant is activ ... Read more

-
The Hacker News
Microsoft Fixes 114 Windows Flaws in January 2026 Patch, One Actively Exploited
Microsoft on Tuesday rolled out its first security update for 2026, addressing 114 security flaws, including one vulnerability that it said has been actively exploited in the wild. Of the 114 flaws, e ... Read more

-
hackread.com
New Dante Spyware Linked to Rebranded Hacking Team, Now Memento Labs
A new global cyber-espionage threat has surfaced with the discovery of Dante, a commercial surveillance tool developed by the Italian company Memento Labs. For your information, Memento Labs is the re ... Read more

-
Kaspersky
Mem3nt0 mori – The Hacking Team is back!
In March 2025, Kaspersky detected a wave of infections that occurred when users clicked on personalized phishing links sent via email. No further action was required to initiate the infection; simply ... Read more

-
TheCyberThrone
Microsoft Patch Tuesday Year 2024 Analysis
In 2024, Microsoft’s Patch Tuesday updates played a critical role in addressing security vulnerabilities across various platforms. Throughout the year, a total of 1,000+ vulnerabilities were patched, ... Read more

-
Kaspersky
APT trends report Q3 2024
Kaspersky’s Global Research and Analysis Team (GReAT) has been releasing quarterly summaries of advanced persistent threat (APT) activity for over seven years now. Based on our threat intelligence res ... Read more

-
Kaspersky
The Crypto Game of Lazarus APT: Investors vs. Zero-days
Introduction Lazarus APT and its BlueNoroff subgroup are a highly sophisticated and multifaceted Korean-speaking threat actor. We closely monitor their activities and quite often see them using their ... Read more

-
Kaspersky
SAS CTF and the many ways to persist a kernel shellcode on Windows 7
SAS 17 Oct 2024 16 minute read On May 18, 2024, Kaspersky’s Global Research & Analysis Team (GReAT), with the help of its partners, held the qualifying stage of the SAS CTF, an international competiti ... Read more

-
Cybersecurity News
RFC 9620: A Call for Human Rights in Internet Protocols
The Internet Research Task Force (IRTF) has released a new document, RFC 9620, aimed at drawing the attention of protocol and architecture developers to critical human rights issues.The document is in ... Read more

-
Cybersecurity News
New Zero-Day Emerges After Microsoft Patch Tuesday: CVE-2024-43461 Targets Windows MSHTML
IE and a promote window dialog appear when the victim double-clicks on the .url file | Image: Check PointIn an unexpected turn of events, Microsoft has revised its September 2024 Patch Tuesday securit ... Read more
-
Cybersecurity News
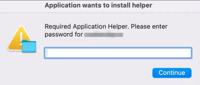
Don’t Fall for the Bait: Poseidon Stealer Masquerades as Sopha AI
Dialog box prompting the user to enter the password | Image: TRUIn a new wave of cyberattacks, macOS users are being targeted by the Poseidon Stealer malware, disguised as an installer for the highly ... Read more

-
Cybersecurity News
CVE-2024-30051: Windows Elevation of Privilege Flaw Exploited by QakBot Malware, PoC Published
Security researchers published the technical details and a proof-of-concept exploit (PoC) code for a zero-day vulnerability in Windows, tracked as CVE-2024-30051, which could allow attackers to escala ... Read more

-
Kaspersky
IT threat evolution Q2 2024
Targeted attacks XZ backdoor: a supply chain attack in the making On March 29, a message on the Openwall oss-security mailing list announced the discovery of a backdoor in XZ, a compression utility in ... Read more
The following table lists the changes that have been made to the
CVE-2024-30051 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 28, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-30051 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-30051 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-30051 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-30051 -
Modified Analysis by [email protected]
Nov. 29, 2024
Action Type Old Value New Value Changed CPE Configuration OR *cpe:2.3:o:microsoft:windows_10_1507:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.10240.20651 *cpe:2.3:o:microsoft:windows_10_1607:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.14393.6981 *cpe:2.3:o:microsoft:windows_10_1607:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.14393.6981 *cpe:2.3:o:microsoft:windows_10_1809:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.5820 *cpe:2.3:o:microsoft:windows_10_21h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.19044.4412 *cpe:2.3:o:microsoft:windows_10_22h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.19045.4412 *cpe:2.3:o:microsoft:windows_11_21h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22000.2960 *cpe:2.3:o:microsoft:windows_11_22h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22621.3593 *cpe:2.3:o:microsoft:windows_11_23h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22631.3593 *cpe:2.3:o:microsoft:windows_server_2016:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.14393.6981 *cpe:2.3:o:microsoft:windows_server_2019:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.5820 *cpe:2.3:o:microsoft:windows_server_2022:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.20348.2458 OR *cpe:2.3:o:microsoft:windows_10_1507:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.10240.20651 *cpe:2.3:o:microsoft:windows_10_1507:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.10240.20651 *cpe:2.3:o:microsoft:windows_10_1607:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.14393.6981 *cpe:2.3:o:microsoft:windows_10_1607:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.14393.6981 *cpe:2.3:o:microsoft:windows_10_1809:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.5820 *cpe:2.3:o:microsoft:windows_10_21h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.19044.4412 *cpe:2.3:o:microsoft:windows_10_22h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.19045.4412 *cpe:2.3:o:microsoft:windows_11_21h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22000.2960 *cpe:2.3:o:microsoft:windows_11_22h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22621.3593 *cpe:2.3:o:microsoft:windows_11_23h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22631.3593 *cpe:2.3:o:microsoft:windows_server_2016:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.14393.6981 *cpe:2.3:o:microsoft:windows_server_2019:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.5820 *cpe:2.3:o:microsoft:windows_server_2022:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.20348.2458 -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-30051 -
CVE Modified by [email protected]
May. 16, 2024
Action Type Old Value New Value -
Initial Analysis by [email protected]
May. 16, 2024
Action Type Old Value New Value Changed Reference Type https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-30051 No Types Assigned https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-30051 Patch, Vendor Advisory Added CWE NIST CWE-787 Added CPE Configuration OR *cpe:2.3:o:microsoft:windows_10_1507:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.10240.20651 *cpe:2.3:o:microsoft:windows_10_1607:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.14393.6981 *cpe:2.3:o:microsoft:windows_10_1607:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.14393.6981 *cpe:2.3:o:microsoft:windows_10_1809:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.5820 *cpe:2.3:o:microsoft:windows_10_21h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.19044.4412 *cpe:2.3:o:microsoft:windows_10_22h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.19045.4412 *cpe:2.3:o:microsoft:windows_11_21h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22000.2960 *cpe:2.3:o:microsoft:windows_11_22h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22621.3593 *cpe:2.3:o:microsoft:windows_11_23h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22631.3593 *cpe:2.3:o:microsoft:windows_server_2016:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.14393.6981 *cpe:2.3:o:microsoft:windows_server_2019:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.5820 *cpe:2.3:o:microsoft:windows_server_2022:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.20348.2458 -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
May. 15, 2024
Action Type Old Value New Value Added Date Added 2024-05-14 Added Due Date 2024-06-04 Added Required Action Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable. Added Vulnerability Name Microsoft DWM Core Library Privilege Escalation Vulnerability -
CVE Received by [email protected]
May. 14, 2024
Action Type Old Value New Value Added Description Windows DWM Core Library Elevation of Privilege Vulnerability Added Reference Microsoft Corporation https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-30051 [No types assigned] Added CWE Microsoft Corporation CWE-122 Added CVSS V3.1 Microsoft Corporation AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H