CVE-2024-43461
Microsoft Windows MSHTML Platform Spoofing Vulnerability - [Actively Exploited]
Description
Windows MSHTML Platform Spoofing Vulnerability
INFO
Published Date :
Sept. 10, 2024, 5:15 p.m.
Last Modified :
Oct. 28, 2025, 2:15 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Microsoft Windows MSHTML Platform contains a user interface (UI) misrepresentation of critical information vulnerability that allows an attacker to spoof a web page. This vulnerability was exploited in conjunction with CVE-2024-38112.
Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
Unknown
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-43461 ; https://nvd.nist.gov/vuln/detail/CVE-2024-43461
Affected Products
The following products are affected by CVE-2024-43461
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Apply the appropriate security update for your operating system.
- Reboot the system if prompted.
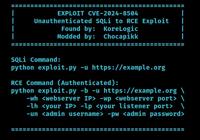
Public PoC/Exploit Available at Github
CVE-2024-43461 has a 1 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-43461.
| URL | Resource |
|---|---|
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-43461 | Patch Vendor Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-43461 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-43461 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-43461
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-43461 vulnerability anywhere in the article.

-
The Cyber Express
Microsoft Patches 117 CVEs: Focus on Critical and Zero-Day Threats
Microsoft has released the October 2024 Patch Tuesday, addressing a total of 117 Common Vulnerabilities and Exposures (CVEs). This month’s Microsoft Patch Tuesday update includes three vulnerabilities ... Read more

-
The Hacker News
Microsoft Issues Security Update Fixing 118 Flaws, Two Actively Exploited in the Wild
Microsoft has released security updates to fix a total of 118 vulnerabilities across its software portfolio, two of which have come under active exploitation in the wild. Of the 118 flaws, three are r ... Read more

-
TheCyberThrone
Microsoft Patch Tuesday – October 2024
Microsoft patched 117 CVEs in October 2024 Patch Tuesday release, with three rated critical, 113 rated important and one rated moderate.27 Elevation of Privilege vulnerabilities7 Security Feature Bypa ... Read more

-
Dark Reading
5 CVEs in Microsoft's October Update to Patch Immediately
Source: fadfebrian via ShutterstockMicrosoft's October security update addressed a substantial 117 vulnerabilities, including two actively exploited flaws and three publicly disclosed but as yet unexp ... Read more

-
Help Net Security
Microsoft patches two zero-days exploited in the wild (CVE-2024-43573, CVE-2024-43572)
For October 2024 Patch Tuesday, Microsoft has released fixes for 117 security vulnerabilities, including two under active exploitation: CVE-2024-43573, a spoofing bug affecting the Windows MSHTML Plat ... Read more

-
tripwire.com
Tripwire Patch Priority Index for September 2024
Tripwire's September 2024 Patch Priority Index (PPI) brings together important vulnerabilities for Microsoft.First on the list are patches for Microsoft Excel, Visio, and Publisher that resolve remote ... Read more

-
Help Net Security
Week in review: Critical VMware vCenter Server bugs fixed, Apple releases iOS 18
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Critical VMware vCenter Server bugs fixed (CVE-2024-38812) Broadcom has released fixes for two vulnera ... Read more

-
Cybersecurity News
RFC 9620: A Call for Human Rights in Internet Protocols
The Internet Research Task Force (IRTF) has released a new document, RFC 9620, aimed at drawing the attention of protocol and architecture developers to critical human rights issues.The document is in ... Read more

-
Help Net Security
PoC exploit for exploited Ivanti Cloud Services Appliance flaw released (CVE-2024-8190)
CVE-2024-8190, an OS command injection vulnerability in Ivanti Cloud Services Appliance (CSA) v4.6, is under active exploitation. Details about the attacks are still unknown, but there may be more in ... Read more

-
TheCyberThrone
CISA KEV Update September 2024 -Part V
The US CISA adds two vulnerabilities to its Known Exploited Vulnerabilities Catalog based on the evidence of active exploitationThe first vulnerability tracked as CVE-2024-43461, Microsoft Windows MSH ... Read more

-
Cybersecurity News
CISA Flags Two Actively Exploited Vulnerabilities: Critical Threats to Windows and WhatsUp Gold
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning, adding two actively exploited security flaws to its Known Exploited Vulnerabilities (KEV) catalog, urging immedia ... Read more
-
Cybersecurity News
Critical Flaws Found in VICIdial Contact Center Suite: CVE-2024-8503 and CVE-2024-8504, PoC Published
In a concerning development for call centers using VICIdial, a popular open-source contact center solution, two high-severity security vulnerabilities have been discovered that could lead to severe da ... Read more

-
The Register
Microsoft confirms IE bug squashed in Patch Tuesday was exploited zero-day
Analysis Microsoft, in a low-key update to its September Patch Tuesday disclosures, has confirmed a just-fixed Internet Explorer vulnerability was exploited as a zero-day before it could be patched. R ... Read more

-
Dark Reading
'Void Banshee' Exploits Second Microsoft Zero-Day
Source: Anucha Cheechang via ShutterstockMicrosoft has recategorized a bug that the company fixed in this month's Patch Tuesday update as a zero-day vulnerability, which the "Void Banshee" advanced pe ... Read more

-
BleepingComputer
CISA warns of Windows flaw used in infostealer malware attacks
CISA has ordered U.S. federal agencies to secure their systems against a recently patched Windows MSHTML spoofing zero-day bug exploited by the Void Banshee APT hacking group. The vulnerability (CVE- ... Read more

-
Help Net Security
Microsoft confirms second 0-day exploited by Void Banshee APT (CVE-2024-43461)
CVE-2024-43461, a spoofing vulnerability affecting Windows MSHTML – a software component used by various apps for rendering render web pages on Windows – “was exploited as a part of an attack chain re ... Read more

-
security.nl
Microsoft bevestigt alsnog actief misbruik van Windows MSHTML-spoofinglek
Een kwetsbaarheid in Windows waarvoor Microsoft vorige week een beveiligingsupdate uitbracht werd voor het uitkomen van de patch actief misbruikt, zo heeft techbedrijf alsnog bevestigd. In eerste inst ... Read more

-
Cybersecurity News
New Zero-Day Emerges After Microsoft Patch Tuesday: CVE-2024-43461 Targets Windows MSHTML
IE and a promote window dialog appear when the victim double-clicks on the .url file | Image: Check PointIn an unexpected turn of events, Microsoft has revised its September 2024 Patch Tuesday securit ... Read more

-
BleepingComputer
Windows vulnerability abused braille “spaces” in zero-day attacks
A recently fixed "Windows MSHTML spoofing vulnerability" tracked under CVE-2024-43461 is now marked as previously exploited after it was used in attacks by the Void Banshee APT hacking group. When fir ... Read more

-
Help Net Security
Week in review: Veeam Backup & Replication RCE could soon be exploited, Microsoft fixes 4 0-days
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Veeam Backup & Replication RCE flaw may soon be leveraged by ransomware gangs (CVE-2024-40711) CVE-202 ... Read more
The following table lists the changes that have been made to the
CVE-2024-43461 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 28, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-43461 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-43461 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-43461 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-43461 -
Initial Analysis by [email protected]
Sep. 17, 2024
Action Type Old Value New Value Changed Reference Type https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-43461 No Types Assigned https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-43461 Patch, Vendor Advisory Added CWE NIST NVD-CWE-Other Added CPE Configuration OR *cpe:2.3:o:microsoft:windows_10_1507:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.10240.20766 *cpe:2.3:o:microsoft:windows_10_1507:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.10240.20766 *cpe:2.3:o:microsoft:windows_10_1607:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.14393.7336 *cpe:2.3:o:microsoft:windows_10_1607:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.14393.7336 *cpe:2.3:o:microsoft:windows_10_1809:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.6293 *cpe:2.3:o:microsoft:windows_10_21h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.19044.4894 *cpe:2.3:o:microsoft:windows_10_22h2:*:*:*:*:*:*:arm64:* versions up to (excluding) 10.0.19045.4894 *cpe:2.3:o:microsoft:windows_10_22h2:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.19045.4894 *cpe:2.3:o:microsoft:windows_10_22h2:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.19045.4894 *cpe:2.3:o:microsoft:windows_11_21h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22000.3197 *cpe:2.3:o:microsoft:windows_11_22h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22621.4169 *cpe:2.3:o:microsoft:windows_11_23h2:*:*:*:*:*:*:arm64:* versions up to (excluding) 10.0.22621.4169 *cpe:2.3:o:microsoft:windows_11_23h2:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.22631.4169 *cpe:2.3:o:microsoft:windows_11_24h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.26100.1742 *cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:x64:* *cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:x86:* *cpe:2.3:o:microsoft:windows_server_2008:r2:*:*:*:*:*:x64:* *cpe:2.3:o:microsoft:windows_server_2012:-:*:*:*:*:*:x64:* *cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:x64:* *cpe:2.3:o:microsoft:windows_server_2016:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.14393.7336 *cpe:2.3:o:microsoft:windows_server_2019:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.6293 *cpe:2.3:o:microsoft:windows_server_2022:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.20348.2700 *cpe:2.3:o:microsoft:windows_server_2022_23h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.25398.1128 -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Sep. 17, 2024
Action Type Old Value New Value Added Date Added 2024-09-16 Added Vulnerability Name Microsoft Windows MSHTML Platform Spoofing Vulnerability Added Due Date 2024-10-07 Added Required Action Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable. -
CVE Received by [email protected]
Sep. 10, 2024
Action Type Old Value New Value Added Description Windows MSHTML Platform Spoofing Vulnerability Added Reference Microsoft Corporation https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-43461 [No types assigned] Added CWE Microsoft Corporation CWE-451 Added CVSS V3.1 Microsoft Corporation AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H