CVE-2025-30401
WhatsApp for Windows MIME Type Spoofing Vulnerability
Description
A spoofing issue in WhatsApp for Windows prior to version 2.2450.6 displayed attachments according to their MIME type but selected the file opening handler based on the attachment’s filename extension. A maliciously crafted mismatch could have caused the recipient to inadvertently execute arbitrary code rather than view the attachment when manually opening the attachment inside WhatsApp. We have not seen evidence of exploitation in the wild.
INFO
Published Date :
April 5, 2025, 12:15 p.m.
Last Modified :
April 9, 2025, 6:15 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | MEDIUM | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Update WhatsApp for Windows to version 2.2450.6 or later.
- Ensure attachments are opened from trusted sources.
- Verify attachment MIME type and filename consistency.
Public PoC/Exploit Available at Github
CVE-2025-30401 has a 3 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-30401.
| URL | Resource |
|---|---|
| https://www.facebook.com/security/advisories/cve-2025-30401 | Third Party Advisory |
| https://www.whatsapp.com/security/advisories/2025/ |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-30401 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-30401
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
GhostPort is a PoC stager demonstrating a Living off the Land (LotL) attack via WhatsApp Web. It exploits trusted messaging vectors and Windows file associations to execute a silent, memory-resident Python payload. Designed for Red Teamers, it bypasses disk-based detection by injecting the Stage-2 payload directly into memory.
Python
None
None
HTML Python Shell
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-30401 vulnerability anywhere in the article.

-
Cyber Security News
New Research Reveals Multiple Attack Surfaces in WeChat & Other Instant Messaging Apps
Instant messaging (IM) applications like WhatsApp, Telegram, WeChat, and QQ have become the “digital arteries” of modern society, facilitating communication for billions of users worldwide. However, t ... Read more

-
The Hacker News
⚡ Weekly Recap: Windows 0-Day, VPN Exploits, Weaponized AI, Hijacked Antivirus and More
Attackers aren't waiting for patches anymore — they are breaking in before defenses are ready. Trusted security tools are being hijacked to deliver malware. Even after a breach is detected and patched ... Read more

-
Cyber Security News
Cybersecurity Weekly Recap: Key Updates on Attacks, Vulnerabilities, & Data Breaches
Welcome to this week’s Cybersecurity Newsletter, providing you with the latest updates and essential insights from the rapidly evolving field of cybersecurity. This edition highlights emerging threats ... Read more

-
Help Net Security
Week in review: Microsoft patches exploited Windows CLFS 0-day, WinRAR MotW bypass flaw fixed
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Microsoft fixes actively exploited Windows CLFS zero-day (CVE-2025-29824) April 2025 Patch Tuesday is ... Read more

-
Help Net Security
FortiSwitch vulnerability may give attackers control over vulnerable devices (CVE-2024-48887)
Fortinet has released patches for flaws affecting many of its products, among them a critical vulnerability (CVE-2024-48887) in its FortiSwitch appliances that could allow unauthenticated attackers to ... Read more

-
Help Net Security
WhatsApp vulnerability could be used to infect Windows users with malware (CVE-2025-30401)
WhatsApp users are urged to update the Windows client app to plug a serious security vulnerability (CVE-2025-30401) that may allow attackers to trick users into running malicious code. Meta classifies ... Read more

-
Daily CyberSecurity
Critical Vulnerabilities: CISA Alerts to Windows CLFS and Gladinet CentreStack Threats
Recently, the Cybersecurity and Infrastructure Security Agency (CISA) added two significant vulnerabilities to its Known Exploited Vulnerabilities Catalog, highlighting the urgency for users to apply ... Read more

-
Daily CyberSecurity
Siemens Security Alert: Critical Vulnerabilities in SENTRON 7KT PAC1260 Data Manager
In a recent security advisory, Siemens ProductCERT has revealed multiple critical vulnerabilities affecting the SENTRON 7KT PAC1260 Data Manager. The advisory, published on April 8, 2025, warns that t ... Read more

-
Daily CyberSecurity
Kibana Code Injection Vulnerability: Prototype Pollution Threat (CVE-2024-12556)
A newly disclosed vulnerability in Kibana, the popular open-source data visualization front-end for Elasticsearch, has been rated CVSS 8.7 due to its potential to allow remote code injection under spe ... Read more

-
Daily CyberSecurity
Chrome Update Fixes High-Severity “Use After Free” Vulnerability
The Chrome Stable channel has been updated to version 135.0.7049.84/.85 for Windows and Mac, and to 135.0.7049.84 for Linux. This update will be rolling out to users over the coming days and weeks. Th ... Read more

-
Daily CyberSecurity
Microsoft April 2025 Patch Tuesday: Critical Security Updates and Zero-Day Exploits
This April, Microsoft’s Patch Tuesday release addresses a significant number of vulnerabilities, highlighting the ever-present need for robust cybersecurity practices. The tech giant rolled out fixes ... Read more

-
Daily CyberSecurity
Apache mod_auth_openidc Vulnerability Exposes Protected Content
In a recently published security advisory, OpenIDC has revealed a vulnerability in mod_auth_openidc, the widely used OpenID Connect module for the Apache HTTP server. The flaw, tracked as CVE-2025-314 ... Read more

-
The Register
Don't open that JPEG in WhatsApp for Windows. It might be an .EXE
A bug in WhatsApp for Windows can be exploited to execute malicious code by anyone crafty enough to persuade a user to open a rigged attachment - and, to be fair, it doesn't take much craft to pull th ... Read more

-
Hackread - Latest Cybersecurity, Tech, AI, Crypto & Hacking News
WhatsApp for Windows Flaw Could Let Hackers Sneak In Malicious Files
A recent security advisory from Facebook Security highlights a spoofing vulnerability tracked as CVE-2025-30401 affecting WhatsApp for Windows. The flaw could have allowed hackers to send malicious at ... Read more

-
BleepingComputer
WhatsApp flaw can let attackers run malicious code on Windows PCs
Meta warned Windows users to update the WhatsApp messaging app to the latest version to patch a vulnerability that can let attackers execute malicious code on their devices. Described as a spoofing is ... Read more

-
Daily CyberSecurity
Fortinet: Critical Unverified Password Change Flaw in FortiSwitch
Fortinet has released a security advisory addressing a critical vulnerability in FortiSwitch products. The vulnerability, identified as CVE-2024-48887 (CVSS 9.3), could allow attackers to gain unautho ... Read more

-
Daily CyberSecurity
Siemens Industrial Edge: Critical Authentication Flaw (CVE-2024-54092)
Siemens has issued security advisories SSA-634640 and SSA-819629 to address a weak authentication vulnerability affecting its Industrial Edge Devices and Industrial Edge Device Kit. The vulnerability, ... Read more

-
security.nl
WhatsApp-spoofinglek kan tot uitvoeren van willekeurige code leiden
Een kwetsbaarheid in WhatsApp voor Windows kan tot het uitvoeren van willekeurige code leiden, zo waarschuwt de chatapplicatie. Het probleem is verholpen in versie 2.2450.6 en is in alle versies daarv ... Read more
-
Daily CyberSecurity
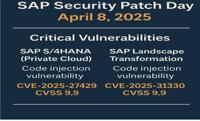
SAP April 2025 Patch Day: Critical Code Injection Risks
The SAP Security Patch Day on April 8, 2025, brought a wave of critical security updates, with a total of 18 new Security Notes and 2 updates to previously released notes. Among the fixes, several add ... Read more

-
Cyber Security News
WhatsApp Vulnerability Let Attackers Execute Malicious Code Via Attachments
A critical vulnerability in WhatsApp for Windows that could allow attackers to execute malicious code through seemingly innocent file attachments. The spoofing vulnerability, officially tracked as CVE ... Read more
The following table lists the changes that have been made to the
CVE-2025-30401 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by [email protected]
Apr. 09, 2025
Action Type Old Value New Value Changed Description A spoofing issue in WhatsApp for Windows prior to version 2.2450.6 displayed attachments according to their MIME type but selected the file opening handler based on the attachment’s filename extension. A maliciously crafted mismatch could have caused the recipient to inadvertently execute arbitrary code rather than view the attachment when manually opening the attachment inside WhatsApp. A spoofing issue in WhatsApp for Windows prior to version 2.2450.6 displayed attachments according to their MIME type but selected the file opening handler based on the attachment’s filename extension. A maliciously crafted mismatch could have caused the recipient to inadvertently execute arbitrary code rather than view the attachment when manually opening the attachment inside WhatsApp. We have not seen evidence of exploitation in the wild. Added Reference https://www.whatsapp.com/security/advisories/2025/ -
Initial Analysis by [email protected]
Apr. 08, 2025
Action Type Old Value New Value Added CWE NVD-CWE-noinfo Added CPE Configuration OR *cpe:2.3:a:whatsapp:whatsapp:*:*:*:*:*:windows:*:* versions up to (excluding) 2.2450.6 Added Reference Type Facebook, Inc.: https://www.facebook.com/security/advisories/cve-2025-30401 Types: Third Party Advisory -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Apr. 07, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:H/PR:L/UI:R/S:U/C:H/I:H/A:L -
New CVE Received by [email protected]
Apr. 05, 2025
Action Type Old Value New Value Added Description A spoofing issue in WhatsApp for Windows prior to version 2.2450.6 displayed attachments according to their MIME type but selected the file opening handler based on the attachment’s filename extension. A maliciously crafted mismatch could have caused the recipient to inadvertently execute arbitrary code rather than view the attachment when manually opening the attachment inside WhatsApp. Added Reference https://www.facebook.com/security/advisories/cve-2025-30401