CVE-2024-45321
"Apache::cpanminus Unsecured HTTP Code Execution Vulnerability"
Description
The App::cpanminus package through 1.7047 for Perl downloads code via insecure HTTP, enabling code execution for network attackers.
INFO
Published Date :
Aug. 27, 2024, 4:15 a.m.
Last Modified :
Dec. 5, 2024, 6:47 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | CRITICAL | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Update the affected perl-App-cpanminus package.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-45321.
| URL | Resource |
|---|---|
| https://github.com/miyagawa/cpanminus/issues/611 | Issue Tracking |
| https://github.com/miyagawa/cpanminus/pull/674 | Issue Tracking Patch |
| https://security.metacpan.org/2024/08/26/cpanminus-downloads-code-using-insecure-http.html | Exploit Third Party Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-45321 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-45321
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-45321 vulnerability anywhere in the article.

-
Daily CyberSecurity
CVE-2025-40909: Perl Threads Vulnerability Exposes File Operation Race Condition
A newly disclosed vulnerability in Perl’s threading mechanism, tracked as CVE-2025-40909, exposes systems to race conditions involving the working directory, potentially enabling local attackers to ma ... Read more
-
Daily CyberSecurity
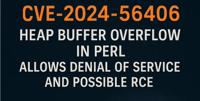
CVE-2024-56406: Heap Overflow Vulnerability in Perl Threatens Denial of Service and Potential Code Execution
Perl, a versatile programming language widely used for various tasks like system administration and web development, has been found to contain a security vulnerability. A recently discovered heap buff ... Read more

-
Cybersecurity News
FreeBSD Issues Critical Security Advisory for CVE-2024-41721 (CVSS 9.8)
A recently disclosed security advisory has unveiled a critical vulnerability affecting FreeBSD’s bhyve hypervisor. Identified as CVE-2024-41721, this flaw carries a CVSS score of 9.8, reflecting its h ... Read more
-
Cybersecurity News
CVE-2024-8698: Keycloak Vulnerability Puts SAML Authentication at Risk
Image: KeycloakIn a concerning development for organizations relying on Keycloak for secure identity and access management, a high-severity vulnerability has been discovered in its SAML signature vali ... Read more

-
Cybersecurity News
New Zero-Day Emerges After Microsoft Patch Tuesday: CVE-2024-43461 Targets Windows MSHTML
IE and a promote window dialog appear when the victim double-clicks on the .url file | Image: Check PointIn an unexpected turn of events, Microsoft has revised its September 2024 Patch Tuesday securit ... Read more
-
Cybersecurity News
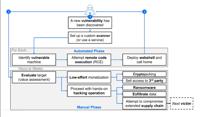
Medusa Exploits Fortinet Flaw (CVE-2023-48788) for Stealthy Ransomware Attacks
A recent report from Bitdefender highlights how Medusa has not only continued its relentless attacks but has also established a unique online presence on both the dark web and the surface web, making ... Read more

-
Cybersecurity News
Hackers target Apache OFBiz RCE flaw CVE-2024-45195 after PoC exploit released
Image: Rapid7According to a report from Imperva, over 25,000 malicious requests targeting 4,000 unique sites have been detected since the CVE-2024-45195 vulnerability in Apache OFBiz was disclosed. Th ... Read more

-
Cybersecurity News
CVE-2024-43491 (CVSS 9.8): Critical Windows 0-Day Flaw Uncovered, Urgent Patching Required
Microsoft has disclosed a critical zero-day vulnerability in its Windows operating system, identified as CVE-2024-43491. The vulnerability, with a severity score of 9.8 (out of 10), resides within the ... Read more

-
Cybersecurity News
Warning: CVE-2024-20469 in Cisco ISE with PoC Code Puts Networks at Risk
A vulnerability, tracked as CVE-2024-20469, has been discovered in Cisco Identity Services Engine (ISE). With a CVSS score of 6.0, this vulnerability allows authenticated, local attackers to elevate p ... Read more

-
Cybersecurity News
Minecraft Server Hit with Record-Breaking 3.15 Billion Packet Rate DDoS Attack
Carpet Bomb attacks aim to flood traffic to all IPs within a subnet on a victim network, with the goal to bypass per destination attack detection | Image: Global Secure LayerGlobal Secure Layer (GSL), ... Read more

-
Cybersecurity News
Critical CVE-2024-45321 Flaw in Popular Perl Module Installer cpanminus, No Patch Available
In a significant security advisory, the Perl community has been alerted to a critical vulnerability, CVE-2024-45321, affecting the widely-used App::cpanminus (cpanm) tool. Rated with a CVSS score of 9 ... Read more
The following table lists the changes that have been made to the
CVE-2024-45321 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Reanalysis by [email protected]
Dec. 05, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H Removed CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H -
Initial Analysis by [email protected]
Sep. 06, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://github.com/miyagawa/cpanminus/issues/611 No Types Assigned https://github.com/miyagawa/cpanminus/issues/611 Issue Tracking Changed Reference Type https://github.com/miyagawa/cpanminus/pull/674 No Types Assigned https://github.com/miyagawa/cpanminus/pull/674 Issue Tracking, Patch Changed Reference Type https://security.metacpan.org/2024/08/26/cpanminus-downloads-code-using-insecure-http.html No Types Assigned https://security.metacpan.org/2024/08/26/cpanminus-downloads-code-using-insecure-http.html Exploit, Third Party Advisory Added CWE NIST CWE-494 Added CPE Configuration OR *cpe:2.3:a:app\:\:cpanminus_project:app\:\:cpanminus:*:*:*:*:*:perl:*:* versions up to (including) 1.7047 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Sep. 06, 2024
Action Type Old Value New Value Added CWE CISA-ADP CWE-494 Removed CWE CISA-ADP CWE-94 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Aug. 27, 2024
Action Type Old Value New Value Added CWE CISA-ADP CWE-94 Added CVSS V3.1 CISA-ADP AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H -
CVE Received by [email protected]
Aug. 27, 2024
Action Type Old Value New Value Added Description The App::cpanminus package through 1.7047 for Perl downloads code via insecure HTTP, enabling code execution for network attackers. Added Reference MITRE https://security.metacpan.org/2024/08/26/cpanminus-downloads-code-using-insecure-http.html [No types assigned] Added Reference MITRE https://github.com/miyagawa/cpanminus/issues/611 [No types assigned] Added Reference MITRE https://github.com/miyagawa/cpanminus/pull/674 [No types assigned]