CVE-2024-38094
Microsoft SharePoint Deserialization Vulnerability - [Actively Exploited]
Description
Microsoft SharePoint Remote Code Execution Vulnerability
INFO
Published Date :
July 9, 2024, 5:15 p.m.
Last Modified :
Oct. 28, 2025, 2:23 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Microsoft SharePoint contains a deserialization vulnerability that allows for remote code execution.
Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
Known Detected Feb 26, 2026
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38094 ; https://nvd.nist.gov/vuln/detail/CVE-2024-38094
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Apply the appropriate security update released by Microsoft.
- If a reboot is requested, restart the SharePoint servers.
Public PoC/Exploit Available at Github
CVE-2024-38094 has a 2 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-38094.
| URL | Resource |
|---|---|
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38094 | Patch Vendor Advisory |
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38094 | Patch Vendor Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-38094 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-38094 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-38094
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
Python CSS JavaScript HTML Jupyter Notebook
None
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-38094 vulnerability anywhere in the article.

-
Daily CyberSecurity
Warlock Ransomware: How a New Group Is Weaponizing Unpatched SharePoint Servers
A newly detailed report from Trend Micro has revealed how the Warlock ransomware group is weaponizing vulnerable Microsoft SharePoint servers in a series of global attacks. The group, which surfaced i ... Read more

-
Daily CyberSecurity
CISA Warns of “ToolShell”: Critical Exploit Chain Hits SharePoint Servers, Bypasses Authentication
The Cybersecurity and Infrastructure Security Agency (CISA) has released an in-depth Malware Analysis Report warning of a sophisticated exploitation campaign targeting on-premises Microsoft SharePoint ... Read more

-
Daily CyberSecurity
Microsoft: China-Backed APTs Actively Exploiting SharePoint Flaws (CVE-2025-49704 & CVE-2025-49706)
Last week, the Microsoft Security Response Center (MSRC) issued an urgent advisory regarding active exploitation of critical vulnerabilities in on-premises SharePoint Server installations. The alert, ... Read more

-
TheCyberThrone
CISA adds CVE-2025-53770 SharePoint Vulnerability to KEV
July 21, 2025SummaryA critical remote code execution (RCE) vulnerability has been discovered in Microsoft SharePoint Server (on-premises versions only). The vulnerability, tracked as CVE-2025-53770, a ... Read more

-
Daily CyberSecurity
ToolShell: New SharePoint RCE Zero-Day Chain Under Active Global Exploitation
Image: CODE WHITE GmbH On the evening of July 18, 2025, Eye Security identified an active, large-scale exploitation of a newly discovered Microsoft SharePoint remote code execution (RCE) vulnerability ... Read more

-
Daily CyberSecurity
SharePoint Server Under Active Zero-Day Attack (CVE-2025-53770, CVSS 9.8), No Patch Yet!
Microsoft has issued an urgent security advisory for on-premises SharePoint Server customers in response to active exploitation of a critical remote code execution (RCE) vulnerability. The issue—now t ... Read more

-
Daily CyberSecurity
Critical RCE Flaws in MICI NetFax Server Unpatched, Vendor Refuses Fix
Image: Rapid7 Security researchers at Rapid7 have uncovered a troubling trio of vulnerabilities in MICI Network Co., Ltd.’s NetFax server (versions < 3.0.1.0), allowing for root-level remote code exec ... Read more

-
Cyber Security News
Microsoft Enhances Exchange & SharePoint Server Security With New Windows Antimalware Scan
Microsoft has announced a significant security upgrade for Exchange Server and SharePoint Server through integration with the Windows Antimalware Scan Interface (AMSI), providing critical protection f ... Read more

-
Cybersecurity News
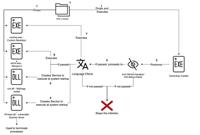
SharePoint Shadow: Havoc’s FUD Malware Conceals Cyber Attacks
Attack flow | Source: FortiGuard LabsA recent report from FortiGuard Labs has shed light on an advanced cyber campaign leveraging the open-source Havoc command-and-control (C2) framework to execute fu ... Read more

-
Cybersecurity News
Five Flaws in Lorex 2K Security Cameras Enable Hackers to Take Full Control, PoC Published
Rapid7’s latest research reveals a series of critical vulnerabilities in the Lorex 2K Indoor Wi-Fi Security Camera, raising significant concerns for consumer security. The vulnerabilities, identified ... Read more
-
Cybersecurity News
Evasive Malware Campaign Leverages CleverSoar Installer & Nidhogg Rootkit
CleverSoar Attack Flow | Image: Rapid7Rapid7 Labs has uncovered a sophisticated malware campaign employing the newly identified CleverSoar installer, a highly evasive threat targeting Chinese and Viet ... Read more

-
Cybersecurity News
Google Chrome Patches High-Severity Flaw CVE-2024-11395 in Latest Stable Release
Google has released a new stable version of its Chrome browser for desktop, addressing three security vulnerabilities, including one high-severity flaw. The update, versions 131.0.6778.85/.86 for Wind ... Read more

-
Cybersecurity News
LodaRAT Strikes Again: New Campaign Targets Global Victims with Updated Capabilities
Researchers at Rapid7 have uncovered a fresh campaign using LodaRAT, a well-known remote access tool (RAT) that has been active since 2016. Initially developed for information gathering, LodaRAT has b ... Read more

-
BleepingComputer
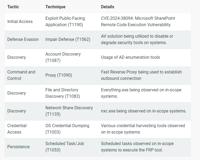
Microsoft SharePoint RCE bug exploited to breach corporate network
A recently disclosed Microsoft SharePoint remote code execution (RCE) vulnerability tracked as CVE-2024-38094 is being exploited to gain initial access to corporate networks. CVE-2024-38094 is a high- ... Read more
-
TheCyberThrone
Microsoft Sharepoint Server CVE-2024-38094 Exploited
Threat actors have exploited a vulnerability in Microsoft SharePoint Server, identified as CVE-2024-38094, allowing them to gain complete domain access and compromise critical systems. The Rapid7 inci ... Read more

-
Cybersecurity News
CVE-2024-38094 Exploited: Attackers Gain Domain Access via Microsoft SharePoint Server
Image: Rapid7A recent report from Rapid7’s Incident Response team reveals a serious compromise of a Microsoft SharePoint server that enabled an attacker to gain entire domain access, impacting critica ... Read more

-
The Hacker News
New Research Reveals Spectre Vulnerability Persists in Latest AMD and Intel Processors
Hardware Security / Vulnerability More than six years after the Spectre security flaw impacting modern CPU processors came to light, new research has found that the latest AMD and Intel processors are ... Read more

-
The Hacker News
THN Cybersecurity Recap: Top Threats, Tools and News (Oct 21 - Oct 27)
Cyber Security / Hacking News Cybersecurity news can sometimes feel like a never-ending horror movie, can't it? Just when you think the villains are locked up, a new threat emerges from the shadows. T ... Read more

-
The Hacker News
Researchers Uncover OS Downgrade Vulnerability Targeting Microsoft Windows Kernel
A new attack technique could be used to bypass Microsoft's Driver Signature Enforcement (DSE) on fully patched Windows systems, leading to operating system (OS) downgrade attacks. "This bypass allows ... Read more

-
Help Net Security
Week in review: Fortinet patches critical FortiManager 0-day, VMware fixes vCenter Server RCE
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Fortinet releases patches for publicly undisclosed critical FortiManager vulnerability In the last cou ... Read more
The following table lists the changes that have been made to the
CVE-2024-38094 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 28, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-38094 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-38094 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-38094 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-38094 -
Modified Analysis by [email protected]
Jan. 27, 2025
Action Type Old Value New Value -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38094 -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Oct. 23, 2024
Action Type Old Value New Value Added Vulnerability Name Microsoft SharePoint Deserialization Vulnerability Added Due Date 2024-11-12 Added Required Action Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable. Added Date Added 2024-10-22 -
Initial Analysis by [email protected]
Jul. 11, 2024
Action Type Old Value New Value Changed Reference Type https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38094 No Types Assigned https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38094 Patch, Vendor Advisory Added CWE NIST CWE-502 Added CPE Configuration OR *cpe:2.3:a:microsoft:sharepoint_server:-:*:*:*:subscription:*:*:* *cpe:2.3:a:microsoft:sharepoint_server:2016:*:*:*:enterprise:*:*:* *cpe:2.3:a:microsoft:sharepoint_server:2019:*:*:*:*:*:*:* -
CVE Received by [email protected]
Jul. 09, 2024
Action Type Old Value New Value Added Description Microsoft SharePoint Remote Code Execution Vulnerability Added Reference Microsoft Corporation https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38094 [No types assigned] Added CWE Microsoft Corporation CWE-502 Added CVSS V3.1 Microsoft Corporation AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H