CVE-2017-0144
Microsoft SMBv1 Remote Code Execution Vulnerability - [Actively Exploited]
Description
The SMBv1 server in Microsoft Windows Vista SP2; Windows Server 2008 SP2 and R2 SP1; Windows 7 SP1; Windows 8.1; Windows Server 2012 Gold and R2; Windows RT 8.1; and Windows 10 Gold, 1511, and 1607; and Windows Server 2016 allows remote attackers to execute arbitrary code via crafted packets, aka "Windows SMB Remote Code Execution Vulnerability." This vulnerability is different from those described in CVE-2017-0143, CVE-2017-0145, CVE-2017-0146, and CVE-2017-0148.
INFO
Published Date :
March 17, 2017, 12:59 a.m.
Last Modified :
April 22, 2026, 1:50 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
The SMBv1 server in multiple Microsoft Windows versions allows remote attackers to execute arbitrary code via crafted packets.
Apply updates per vendor instructions.
Known Detected Feb 10, 2022
https://nvd.nist.gov/vuln/detail/CVE-2017-0144
Affected Products
The following products are affected by CVE-2017-0144
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 2.0 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Apply the appropriate Microsoft security updates.
- Disable SMBv1.
Public PoC/Exploit Available at Github
CVE-2017-0144 has a 565 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2017-0144.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2017-0144 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2017-0144
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Mapping Network Tool — 2026 level Python network scanner
Python Shell
Python tool to scan home network for open ports, CVEs and vulnerabilities. Includes continuous device monitor, CVE lookup, and HTML/JSON/CSV reports.
cve cybersecurity ethical-hacking home-network network-security port-scanner python python3 security-tools vulnerability-scanner
Python
Objective: Use free tools to identify common vulnerabilities on your computer. Tools: OpenVAS Community Edition (free vulnerability scanner) or Nessus Essentials. Deliverables: Vulnerability scan report with identified issues.
My Internship Repository
Autonomous Red Team AI - Nmap + CVE + LLM Pipeline | ~60% recon time reduction | Tested on DVWA, Metasploitable2, HackTheBox
Python HTML Batchfile Shell
Pentest Simluation on Happy Accident Labs
A comprehensive academic and technical malware analysis of the NotPetya cyberattack
A security research framework designed to map CVE profiles against telemetry policies (Sigma/YARA) to programmatically expose corporate detection gaps and output structured feature data for AI model ingestion.
Python
A Python-based network scanner that performs SYN port scanning, banner grabbing, service detection, and basic CVE vulnerability identification using Scapy and socket programming.
Python
None
None
Python Shell HTML
None
Python HTML Shell
None
None
HTB - Blue
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2017-0144 vulnerability anywhere in the article.

-
AttackIQ
Ransom Tales: Volume VI — Throwback Edition! Emulating Ryuk, Conti, and BlackCat Ransomware
On July 22, 2025, AttackIQ introduced Ransom Tales, an initiative focused on routinely emulating the Tactics, Techniques, and Procedures (TTPs) associated with the prolific ransomware families current ... Read more

-
TheCyberThrone
CEH v13 Detailed Notes Part II
Introduction (Modules 4–6)Modules 4–6 of CEH v13 take us from understanding how attackers enumerate systems (gathering detailed system-level data) all the way to actively hacking into those systems an ... Read more

-
Huntress
Ten Years of Resilience, Innovation & Community-Driven Defense
The world of cybersecurity has been a wild ride over the last decade. As attackers stepped up their game year over year, the security community responded and adapted with resilience and ingenuity to e ... Read more

-
CybersecurityNews
Threat Actors Abuse Microsoft Help Index File to Execute PipeMagic Malware
Cybersecurity researchers have uncovered a sophisticated malware campaign exploiting Microsoft Help Index Files (.mshi) to deliver the notorious PipeMagic backdoor, marking a significant evolution in ... Read more

-
Daily CyberSecurity
PipeMagic Returns: Kaspersky Uncovers Evolving Backdoor Linked to CVE-2025-29824 Exploits
Kaspersky Labs has released a new report shedding light on the persistent threat posed by PipeMagic, a sophisticated backdoor that has resurfaced in recent attacks against organizations in Saudi Arabi ... Read more

-
The Hacker News
Microsoft Windows Vulnerability Exploited to Deploy PipeMagic RansomExx Malware
Aug 18, 2025Ravie LakshmananVulnerability / Cloud Security Cybersecurity researchers have lifted the lid on the threat actors' exploitation of a now-patched security flaw in Microsoft Windows to dep ... Read more

-
Kaspersky
Evolution of the PipeMagic backdoor: from the RansomExx incident to CVE-2025-29824
In April 2025, Microsoft patched 121 vulnerabilities in its products. According to the company, only one of them was being used in real-world attacks at the time the patch was released: CVE-2025-29824 ... Read more

-
The Cloudflare Blog
Cloudflare protects against critical SharePoint vulnerability, CVE-2025-53770
2025-07-223 min readOn July 19, 2025, Microsoft disclosed CVE-2025-53770, a critical zero-day Remote Code Execution (RCE) vulnerability. Assigned a CVSS 3.1 base score of 9.8 (Critical), the vulnerabi ... Read more

-
Cyber Security News
Active Directory Attack Kill Chain Checklist & Tools List- 2025
The “Active Directory Kill Chain Attack & Defense” concept is a structured approach to understanding the sequence of events or stages involved in an Active Directory (AD) attack and the corresponding ... Read more

-
Cybersecurity News
LemonDuck Exploits EternalBlue Vulnerability for Cryptomining Attacks
A recent report from security researchers at Aufa and NetbyteSEC Interns sheds light on the resurgence of the LemonDuck malware, which is now exploiting the EternalBlue vulnerability (CVE-2017-0144) i ... Read more
-
Cybersecurity News
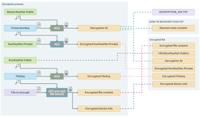
CosmicBeetle’s ScRansom Ransomware: A Growing Threat to European and Asian Businesses
Encryption scheme utilized by the latest ScRansom samples | Image: ESETIn a significant development tracked by ESET researchers, the threat actor known as CosmicBeetle has intensified its ransomware o ... Read more

-
The Hacker News
CosmicBeetle Deploys Custom ScRansom Ransomware, Partnering with RansomHub
The threat actor known as CosmicBeetle has debuted a new custom ransomware strain called ScRansom in attacks targeting small- and medium-sized businesses (SMBs) in Europe, Asia, Africa, and South Amer ... Read more

-
BleepingComputer
NoName ransomware gang deploying RansomHub malware in recent attacks
The NoName ransomware gang has been trying to build a reputation for more than three years targeting small and medium-sized businesses worldwide with its encryptors and may now be working as a RansomH ... Read more

-
The Register
RansomHub hits 210 victims in just 6 months
As RansomHub continues to scoop up top talent from the fallen LockBit and ALPHV operations while accruing a smorgasbord of victims, security and law enforcement agencies in the US feel it's time to is ... Read more
The following table lists the changes that have been made to the
CVE-2017-0144 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Apr. 22, 2026
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2017-0144 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 22, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2017-0144 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2017-0144 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2017-0144 -
Modified Analysis by [email protected]
Apr. 04, 2025
Action Type Old Value New Value Changed CPE Configuration AND OR *cpe:2.3:a:microsoft:server_message_block:1.0:*:*:*:*:*:*:* OR cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_8.1:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2016:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_rt_8.1:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_vista:-:sp2:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2012:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_10_1607:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_10_1511:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_10_1507:-:*:*:*:*:*:*:* AND OR *cpe:2.3:a:microsoft:server_message_block:1.0:*:*:*:*:*:*:* OR cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_8.1:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2016:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_rt_8.1:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_vista:-:sp2:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2012:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_10_1507:-:*:*:*:*:*:x64:* cpe:2.3:o:microsoft:windows_10_1507:-:*:*:*:*:*:x86:* cpe:2.3:o:microsoft:windows_10_1511:-:*:*:*:*:*:x64:* cpe:2.3:o:microsoft:windows_10_1511:-:*:*:*:*:*:x86:* cpe:2.3:o:microsoft:windows_10_1607:-:*:*:*:*:*:x64:* cpe:2.3:o:microsoft:windows_10_1607:-:*:*:*:*:*:x86:* -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Feb. 10, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H -
Modified Analysis by [email protected]
Feb. 04, 2025
Action Type Old Value New Value -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference http://packetstormsecurity.com/files/154690/DOUBLEPULSAR-Payload-Execution-Neutralization.html Added Reference http://packetstormsecurity.com/files/156196/SMB-DOUBLEPULSAR-Remote-Code-Execution.html Added Reference http://www.securityfocus.com/bid/96704 Added Reference http://www.securitytracker.com/id/1037991 Added Reference https://cert-portal.siemens.com/productcert/pdf/ssa-701903.pdf Added Reference https://cert-portal.siemens.com/productcert/pdf/ssa-966341.pdf Added Reference https://ics-cert.us-cert.gov/advisories/ICSMA-18-058-02 Added Reference https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-0144 Added Reference https://www.exploit-db.com/exploits/41891/ Added Reference https://www.exploit-db.com/exploits/41987/ Added Reference https://www.exploit-db.com/exploits/42030/ Added Reference https://www.exploit-db.com/exploits/42031/ -
Modified Analysis by [email protected]
Jul. 24, 2024
Action Type Old Value New Value Removed CVSS V3 NIST AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H Added CVSS V3.1 NIST AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Changed Reference Type http://packetstormsecurity.com/files/154690/DOUBLEPULSAR-Payload-Execution-Neutralization.html No Types Assigned http://packetstormsecurity.com/files/154690/DOUBLEPULSAR-Payload-Execution-Neutralization.html Exploit, Third Party Advisory, VDB Entry Changed Reference Type http://packetstormsecurity.com/files/156196/SMB-DOUBLEPULSAR-Remote-Code-Execution.html No Types Assigned http://packetstormsecurity.com/files/156196/SMB-DOUBLEPULSAR-Remote-Code-Execution.html Exploit, Third Party Advisory, VDB Entry Changed Reference Type http://www.securityfocus.com/bid/96704 No Types Assigned http://www.securityfocus.com/bid/96704 Broken Link, Third Party Advisory, VDB Entry Changed Reference Type http://www.securitytracker.com/id/1037991 No Types Assigned http://www.securitytracker.com/id/1037991 Broken Link, Third Party Advisory, VDB Entry Changed Reference Type https://cert-portal.siemens.com/productcert/pdf/ssa-701903.pdf No Types Assigned https://cert-portal.siemens.com/productcert/pdf/ssa-701903.pdf Third Party Advisory Changed Reference Type https://cert-portal.siemens.com/productcert/pdf/ssa-966341.pdf No Types Assigned https://cert-portal.siemens.com/productcert/pdf/ssa-966341.pdf Third Party Advisory Changed Reference Type https://ics-cert.us-cert.gov/advisories/ICSMA-18-058-02 No Types Assigned https://ics-cert.us-cert.gov/advisories/ICSMA-18-058-02 Third Party Advisory, US Government Resource Changed Reference Type https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-0144 Vendor Advisory https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-0144 Patch, Vendor Advisory Changed Reference Type https://www.exploit-db.com/exploits/41891/ No Types Assigned https://www.exploit-db.com/exploits/41891/ Exploit, Third Party Advisory, VDB Entry Changed Reference Type https://www.exploit-db.com/exploits/41987/ No Types Assigned https://www.exploit-db.com/exploits/41987/ Exploit, Third Party Advisory, VDB Entry Changed Reference Type https://www.exploit-db.com/exploits/42030/ No Types Assigned https://www.exploit-db.com/exploits/42030/ Exploit, Third Party Advisory, VDB Entry Changed Reference Type https://www.exploit-db.com/exploits/42031/ No Types Assigned https://www.exploit-db.com/exploits/42031/ Exploit, Third Party Advisory, VDB Entry Removed CWE NIST CWE-20 Added CWE NIST NVD-CWE-noinfo Changed CPE Configuration AND OR *cpe:2.3:a:microsoft:server_message_block:1.0:*:*:*:*:*:*:* OR cpe:2.3:o:microsoft:windows_10:*:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_10:1511:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_10:1607:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_8.1:*:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_rt_8.1:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2012:-:gold:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2016:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_vista:-:sp2:*:*:*:*:*:* AND OR *cpe:2.3:a:microsoft:server_message_block:1.0:*:*:*:*:*:*:* OR cpe:2.3:o:microsoft:windows_10_1507:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_10_1511:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_10_1607:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_8.1:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_rt_8.1:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2012:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2016:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_vista:-:sp2:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:siemens:acuson_p300_firmware:13.02:*:*:*:*:*:*:* *cpe:2.3:o:siemens:acuson_p300_firmware:13.03:*:*:*:*:*:*:* *cpe:2.3:o:siemens:acuson_p300_firmware:13.20:*:*:*:*:*:*:* *cpe:2.3:o:siemens:acuson_p300_firmware:13.21:*:*:*:*:*:*:* OR cpe:2.3:h:siemens:acuson_p300:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:siemens:acuson_p500_firmware:va10:*:*:*:*:*:*:* *cpe:2.3:o:siemens:acuson_p500_firmware:vb10:*:*:*:*:*:*:* OR cpe:2.3:h:siemens:acuson_p500:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:siemens:acuson_sc2000_firmware:*:*:*:*:*:*:*:* versions from (including) 4.0 up to (excluding) 4.0e *cpe:2.3:o:siemens:acuson_sc2000_firmware:5.0a:*:*:*:*:*:*:* OR cpe:2.3:h:siemens:acuson_sc2000:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:siemens:acuson_x700_firmware:1.0:*:*:*:*:*:*:* *cpe:2.3:o:siemens:acuson_x700_firmware:1.1:*:*:*:*:*:*:* OR cpe:2.3:h:siemens:acuson_x700:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:siemens:syngo_sc2000_firmware:*:*:*:*:*:*:*:* versions from (including) 4.0 up to (excluding) 4.0e *cpe:2.3:o:siemens:syngo_sc2000_firmware:5.0a:*:*:*:*:*:*:* OR cpe:2.3:h:siemens:syngo_sc2000:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:siemens:tissue_preparation_system_firmware:*:*:*:*:*:*:*:* OR cpe:2.3:h:siemens:tissue_preparation_system:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:siemens:versant_kpcr_molecular_system_firmware:*:*:*:*:*:*:*:* OR cpe:2.3:h:siemens:versant_kpcr_molecular_system:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:siemens:versant_kpcr_sample_prep_firmware:*:*:*:*:*:*:*:* OR cpe:2.3:h:siemens:versant_kpcr_sample_prep:-:*:*:*:*:*:*:* -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CVE Modified by [email protected]
Feb. 04, 2020
Action Type Old Value New Value Added Reference http://packetstormsecurity.com/files/156196/SMB-DOUBLEPULSAR-Remote-Code-Execution.html [No Types Assigned] -
CVE Modified by [email protected]
Oct. 01, 2019
Action Type Old Value New Value Added Reference http://packetstormsecurity.com/files/154690/DOUBLEPULSAR-Payload-Execution-Neutralization.html [No Types Assigned] -
CVE Modified by [email protected]
Jun. 21, 2018
Action Type Old Value New Value Added Reference https://cert-portal.siemens.com/productcert/pdf/ssa-966341.pdf [No Types Assigned] -
CVE Modified by [email protected]
May. 11, 2018
Action Type Old Value New Value Added Reference https://cert-portal.siemens.com/productcert/pdf/ssa-701903.pdf [No Types Assigned] -
CVE Modified by [email protected]
Mar. 28, 2018
Action Type Old Value New Value Added Reference https://ics-cert.us-cert.gov/advisories/ICSMA-18-058-02 [No Types Assigned] -
CVE Modified by [email protected]
Aug. 16, 2017
Action Type Old Value New Value Added Reference https://www.exploit-db.com/exploits/41987/ [No Types Assigned] Added Reference https://www.exploit-db.com/exploits/41891/ [No Types Assigned] -
CVE Modified by [email protected]
Aug. 13, 2017
Action Type Old Value New Value Added Reference https://www.exploit-db.com/exploits/42031/ [No Types Assigned] Added Reference https://www.exploit-db.com/exploits/42030/ [No Types Assigned] -
CVE Modified by [email protected]
Jul. 17, 2017
Action Type Old Value New Value Added Reference http://www.securitytracker.com/id/1037991 [No Types Assigned] -
CVE Modified by [email protected]
Mar. 18, 2017
Action Type Old Value New Value Added Reference http://www.securityfocus.com/bid/96704 [No Types Assigned] -
Initial Analysis by [email protected]
Mar. 17, 2017
Action Type Old Value New Value Added CVSS V2 (AV:N/AC:M/Au:N/C:C/I:C/A:C) Added CVSS V3 AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-0144 No Types Assigned https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-0144 Vendor Advisory Added CWE CWE-20 Added CPE Configuration AND OR *cpe:2.3:a:microsoft:server_message_block:1.0:*:*:*:*:*:*:* OR cpe:2.3:o:microsoft:windows_10:*:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_10:1511:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_10:1607:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_8.1:*:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_rt_8.1:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2012:-:gold:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_server_2016:-:*:*:*:*:*:*:* cpe:2.3:o:microsoft:windows_vista:-:sp2:*:*:*:*:*:*