CVE-2024-6678
Authentication Bypass by Spoofing in GitLab
Description
An issue was discovered in GitLab CE/EE affecting all versions starting from 8.14 prior to 17.1.7, starting from 17.2 prior to 17.2.5, and starting from 17.3 prior to 17.3.2, which allows an attacker to trigger a pipeline as an arbitrary user under certain circumstances.
INFO
Published Date :
Sept. 12, 2024, 7:15 p.m.
Last Modified :
Nov. 21, 2024, 9:50 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
Solution
- There is no known solution at this time.
Public PoC/Exploit Available at Github
CVE-2024-6678 has a 2 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-6678.
| URL | Resource |
|---|---|
| https://gitlab.com/gitlab-org/gitlab/-/issues/471923 | Broken Link |
| https://hackerone.com/reports/2595495 | Permissions Required |
| https://about.gitlab.com/releases/2024/09/11/patch-release-gitlab-17-3-2-released/ |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-6678 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-6678
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
PoC for CVE-2024-6678
Python
CVE POC repo 자동 수집기
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-6678 vulnerability anywhere in the article.

-
Cybersecurity News
LemonDuck Exploits EternalBlue Vulnerability for Cryptomining Attacks
A recent report from security researchers at Aufa and NetbyteSEC Interns sheds light on the resurgence of the LemonDuck malware, which is now exploiting the EternalBlue vulnerability (CVE-2017-0144) i ... Read more
-
Cybersecurity News
Threat Actors Exploit HR-Related Phishing Tactics in Sophisticated Credential-Stealing Campaigns
Image: CofensePhishing attacks continue to evolve in complexity, and the latest report from the Cofense Phishing Defense Center highlights a troubling trend: cybercriminals are increasingly using HR-r ... Read more

-
Dark Reading
GitLab Warns of Max Severity Authentication Bypass Bug
Source: T. Schneider via ShutterstockOrganizations with self-hosted GitLab instances configured for SAML-based authentication might want to update immediately to new versions of the DevOps platform th ... Read more

-
Cybersecurity News
The Safe C++ Extensions Proposal: Strengthening Security in a Complex Ecosystem
In a decisive move to address long-standing memory safety concerns, the C++ community has unveiled the Safe C++ Extensions proposal, marking a crucial moment for the language. After two years of in-de ... Read more

-
Cybersecurity News
166k+ Projects at Risk: AutoGPT’s Critical Vulnerability Explained – CVE-2024-6091 (CVSS 9.8)
A significant security vulnerability has been discovered in AutoGPT, a powerful AI tool designed to automate tasks through intelligent agents. With over 166k stars on GitHub, AutoGPT has gained popula ... Read more
-
Cybersecurity News
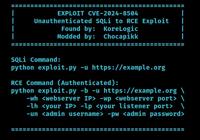
Critical Flaws Found in VICIdial Contact Center Suite: CVE-2024-8503 and CVE-2024-8504, PoC Published
In a concerning development for call centers using VICIdial, a popular open-source contact center solution, two high-severity security vulnerabilities have been discovered that could lead to severe da ... Read more
-
Cybersecurity News
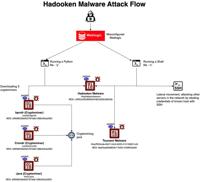
Hadooken Malware: A New Threat to WebLogic Servers
The entire attack flow | Image: Aqua NautilusCybersecurity researchers at Aqua Nautilus have discovered a new Linux malware strain, dubbed “Hadooken,” that is specifically targeting Oracle WebLogic se ... Read more

-
The Register
23andMe settles class-action breach lawsuit for $30 million
Infosec In Brief Genetic testing outfit 23andMe has settled a proposed class action case related to a 2023 data breach for $30 million. Documents [PDF] filed in a San Francisco federal court last Thur ... Read more

-
TheCyberThrone
Solarwinds fixes CVE-2024-28990 & CVE-2024-28991 in ARM Product
SolarWinds has released patches for two vulnerabilities affecting their Access Rights Manager (ARM) software, that have the potential to compromise the security of networks utilizing ARM, with impacts ... Read more

-
TheCyberThrone
Apache OFBiz Vulnerability CVE-2024-45195 actively exploited
Apache OFBiz has got a security update for a flaw CVE-2024-45195 with a CVSS score of 7.5 that allows attackers to bypass authorization checks and execute arbitrary code on the server, even without v ... Read more

-
TheCyberThrone
PaloAlto fixes CVE-2024-8686 and CVE-2024-8687
Palo Alto released patches to address several vulnerabilities discovered in their products, if exploited, could allow unauthorized access, data breaches, and disruption of services.A range of vulnerab ... Read more

-
The Hacker News
Urgent: GitLab Patches Critical Flaw Allowing Unauthorized Pipeline Job Execution
DevSecOps / Vulnerability GitLab on Wednesday released security updates to address 17 security vulnerabilities, including a critical flaw that allows an attacker to run pipeline jobs as an arbitrary u ... Read more

-
TheCyberThrone
GitLab fixes several vulnerabilities including CVE-2024-6678
GitLab has released critical security patches for its Community Edition (CE) and Enterprise Edition (EE) that could allow an attacker to execute arbitrary code.Vulnerability detailsCVE-2024-6678 with ... Read more

-
BleepingComputer
GitLab warns of critical pipeline execution vulnerability
GitLab has released critical updates to address multiple vulnerabilities, the most severe of them (CVE-2024-6678) allowing an attacker to trigger pipelines as arbitrary users under certain conditions. ... Read more

-
The Cyber Express
GitLab Issues Critical Patch Releases: Versions 17.3.2, 17.2.5, and 17.1.7 Address Key Vulnerabilities
GitLab has released critical patch updates across its Community Edition (CE) and Enterprise Edition (EE) to address security vulnerabilities and bugs. The GitLab critical patch release includes vital ... Read more

-
security.nl
GitLab waarschuwt voor kritiek lek dat aanvaller pipeline laat uitvoeren
De populaire online DevOps-tool GitLab waarschuwt voor een kritieke kwetsbaarheid waardoor een aanvaller in bepaalde gevallen als willekeurige gebruiker een pipeline kan uitvoeren. De impact van het b ... Read more
-
Cybersecurity News
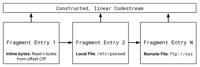
Critical Vulnerabilities in Kakadu JPEG 2000 Library Expose Systems to Remote Attacks
Image: CVRResearchers from the Google Chrome Vulnerability Rewards (CVR) team have identified a series of critical vulnerabilities within the Kakadu image library, a widely deployed software component ... Read more

-
Cybersecurity News
GitLab Issues Critical Security Patch for CVE-2024-6678 (CVSS 9.9), Urges Immediate Update
In a recent security advisory, GitLab announced the release of critical security patches for its Community Edition (CE) and Enterprise Edition (EE). The patches address several vulnerabilities, includ ... Read more
The following table lists the changes that have been made to the
CVE-2024-6678 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://about.gitlab.com/releases/2024/09/11/patch-release-gitlab-17-3-2-released/ -
Initial Analysis by [email protected]
Sep. 18, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://gitlab.com/gitlab-org/gitlab/-/issues/471923 No Types Assigned https://gitlab.com/gitlab-org/gitlab/-/issues/471923 Broken Link Changed Reference Type https://hackerone.com/reports/2595495 No Types Assigned https://hackerone.com/reports/2595495 Permissions Required Added CWE NIST CWE-290 Added CPE Configuration OR *cpe:2.3:a:gitlab:gitlab:*:*:*:*:community:*:*:* versions from (including) 8.14.0 up to (excluding) 17.1.7 *cpe:2.3:a:gitlab:gitlab:*:*:*:*:enterprise:*:*:* versions from (including) 8.14.0 up to (excluding) 17.1.7 *cpe:2.3:a:gitlab:gitlab:*:*:*:*:community:*:*:* versions from (including) 17.2.0 up to (excluding) 17.2.5 *cpe:2.3:a:gitlab:gitlab:*:*:*:*:enterprise:*:*:* versions from (including) 17.2.0 up to (excluding) 17.2.5 *cpe:2.3:a:gitlab:gitlab:*:*:*:*:community:*:*:* versions from (including) 17.3.0 up to (excluding) 17.3.2 *cpe:2.3:a:gitlab:gitlab:*:*:*:*:enterprise:*:*:* versions from (including) 17.3.0 up to (excluding) 17.3.2 -
CVE Received by [email protected]
Sep. 12, 2024
Action Type Old Value New Value Added Description An issue was discovered in GitLab CE/EE affecting all versions starting from 8.14 prior to 17.1.7, starting from 17.2 prior to 17.2.5, and starting from 17.3 prior to 17.3.2, which allows an attacker to trigger a pipeline as an arbitrary user under certain circumstances. Added Reference GitLab Inc. https://gitlab.com/gitlab-org/gitlab/-/issues/471923 [No types assigned] Added Reference GitLab Inc. https://hackerone.com/reports/2595495 [No types assigned] Added CWE GitLab Inc. CWE-290 Added CVSS V3.1 GitLab Inc. AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H