CVE-2024-4577
PHP-CGI OS Command Injection Vulnerability - [Actively Exploited]
Description
In PHP versions 8.1.* before 8.1.29, 8.2.* before 8.2.20, 8.3.* before 8.3.8, when using Apache and PHP-CGI on Windows, if the system is set up to use certain code pages, Windows may use "Best-Fit" behavior to replace characters in command line given to Win32 API functions. PHP CGI module may misinterpret those characters as PHP options, which may allow a malicious user to pass options to PHP binary being run, and thus reveal the source code of scripts, run arbitrary PHP code on the server, etc.
INFO
Published Date :
June 9, 2024, 8:15 p.m.
Last Modified :
Nov. 3, 2025, 7:23 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
PHP, specifically Windows-based PHP used in CGI mode, contains an OS command injection vulnerability that allows for arbitrary code execution. This vulnerability is a patch bypass for CVE-2012-1823.
Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
Known Detected Jun 12, 2024
This vulnerability affects a common open-source component, third-party library, or a protocol used by different products. Please check with specific vendors for information on patching status. For more information, please see: https://www.php.net/ChangeLog-8.php#; https://nvd.nist.gov/vuln/detail/CVE-2024-4577
Affected Products
The following products are affected by CVE-2024-4577
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Update the PHP package.
- Upgrade to PHP version 8.1.29, 8.2.20, or 8.3.8 or later.
Public PoC/Exploit Available at Github
CVE-2024-4577 has a 211 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-4577.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-4577 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-4577
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
CVE pažeidžiamumų analizė lietuvių kalba
Necromancer suite: hellhound (offensive security tool)
Python
None
Python JavaScript HTML CSS Batchfile Shell
A collection of CVE reproductions with proof-of-concept code, technical analyses, and detailed write-ups. For defensive research and educational purposes.
Python Java Ruby Shell Dockerfile PHP C
HoneyLabs MCP server — query 90 days of honeypot probe data from Claude, Cursor, Gemini, Cline. Free tier 500 credits/day.
Dockerfile Python
HuntingYuk custom Suricata detection rules (low-FP, PoC-proven)
Shell Python
Automated detection & exploitation of critical PHP vulnerabilities (CVE-2024-4577 bypass, CVE-2025-14177, CVE-2025-14180, CVE-2025-14178)
Shell
🛡️ AI-powered EDR for air-gapped environments. Pre-release showcase. Source coming when production-ready.
air-gapped cybersecurity edr endpoint-security gemma llm local-ai mitre-attack rust security threat-detection xdr
OSINT-X Dashboard
HTML
None
Go HTML JavaScript CSS TypeScript
HTTP honeypot on autopilot
canarytokens deception deception-technology honeypot honeypots codex llm-security openai
Python
None
HTML
Mudasir Zia — Cybersecurity Student | Bug Bounty Hunter | Web Developer | Mansehra, Pakistan
Autonomous AI-Powered Security Reconnaissance Platform - Self-hosted LLM + 40+ pentesting tools + Docker sandbox
Python Dockerfile HTML
Penetration testing Cheat Sheet with tools
Python C Shell PHP PowerShell ASP.NET
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-4577 vulnerability anywhere in the article.
-
Daily CyberSecurity
Cyber Escalation in the Middle East: Disruption, Deception, and the Quest for Data
A new report from Rapid7 Labs highlights a significant spike in retaliatory cyber activity targeting both regional and Western infrastructure, characterized by a mix of state-directed espionage and a ... Read more

-
Daily CyberSecurity
Coordinated Cryptojacking Blitz: Hackers Exploit ThinkPHP and PHP RCE Flaws to Maximize Mining Profit
Analysts at GreyNoise Intelligence have reported a sharp, coordinated surge in attacks exploiting vulnerabilities across PHP and its frameworks—including ThinkPHP, PHPUnit, and the recently disclosed ... Read more

-
Cyber Security News
“CitrixBleed 2” Vulnerability PoC Released – Warns of Potential Widespread Exploitation
Critical flaw in Citrix NetScaler devices echoes infamous 2023 security breach that crippled major organizations worldwide. The new critical vulnerability in Citrix NetScaler devices has security expe ... Read more

-
Daily CyberSecurity
Amazon Shuts Down Freevee: What’s Next for Free Streaming on Prime Video?
Amazon has announced that it will shut down its free streaming service, Freevee, this August, with all content set to be migrated to its subscription-based platform, Prime Video. However, the company ... Read more

-
Cyber Security News
Lockbit Ransomware Hacked – Leaked Database Exposes Internal Chats
The notorious LockBit ransomware operation has suffered a significant breach. Attackers defaced their dark web infrastructure and leaking a comprehensive database containing sensitive operational deta ... Read more

-
BleepingComputer
LockBit ransomware gang hacked, victim negotiations exposed
The LockBit ransomware gang has suffered a data breach after its dark web affiliate panels were defaced and replaced with a message linking to a MySQL database dump. All of the ransomware gang's admin ... Read more

-
Cybersecurity News
Amazon Prime Phishing Scam Steals Login, Payment Info
The Cofense Phishing Defense Center (PDC) has identified a new phishing campaign that specifically targets Amazon Prime users, attempting to steal login credentials, security answers, and payment deta ... Read more

-
The Cyber Express
December 2024 Cyble Report: Malware, Phishing, and IoT Vulnerabilities on the Rise
The latest Sensor Intelligence Report from Cyble, dated December 4–10, 2024, sheds light on a troubling increase in cyber threats, including malware intrusions, phishing scams, and attacks targeting v ... Read more

-
Cybersecurity News
PoC Exploit Code Releases Cleo Zero-Day Vulnerability (CVE-2024-50623)
Organizations using Cleo file transfer software are urged to take immediate action as a critical vulnerability, CVE-2024-50623, is being actively exploited in the wild. This zero-day flaw affects Cleo ... Read more

-
The Hacker News
AndroxGh0st Malware Integrates Mozi Botnet to Target IoT and Cloud Services
IoT Security / Vulnerability The threat actors behind the AndroxGh0st malware are now exploiting a broader set of security flaws impacting various internet-facing applications, while also deploying th ... Read more

-
The Cyber Express
Cyble Sensors Uncover Cyberattacks on Java Framework and IoT Devices
Cyble vulnerability intelligence unit has shared a report, detailing the recent cyberattacks on the Spring Java framework and hundreds of thousands of Internet of Things (IoT) devices. The report shed ... Read more

-
The Cyber Express
Progress Telerik, Cisco, QNAP and Linux Under Attack: Cyble Honeypot Sensors
Cyble’s Vulnerability Intelligence unit has detected cyberattacks on several key IT products and systems, as threat actors have been quick to exploit vulnerabilities and enterprises slow to patch them ... Read more

-
Cybersecurity News
LemonDuck Exploits EternalBlue Vulnerability for Cryptomining Attacks
A recent report from security researchers at Aufa and NetbyteSEC Interns sheds light on the resurgence of the LemonDuck malware, which is now exploiting the EternalBlue vulnerability (CVE-2017-0144) i ... Read more

-
Cybersecurity News
Linux Servers Under Siege: “Perfctl” Malware Evades Detection for Years
The entire attack flow | Image: Aqua NautilusIn a recent report by Aqua Nautilus researchers Assaf Morag and Idan Revivo, the Linux server community has been alerted to the presence of a particularly ... Read more

-
Cybersecurity News
Multiple Vulnerabilities Discovered in PHP, Prompting Urgent Security Updates
The PHP project has recently released a security advisory, addressing several vulnerabilities affecting various versions of PHP. These vulnerabilities range from potential log tampering to arbitrary f ... Read more

-
Cybersecurity News
Cyberattack on Delta Prime: Losses Soar to $6M
The Delta Prime platform fell victim to a cyberattack resulting in the theft of cryptocurrency worth approximately $6 million. Initially, losses were reported at around $4.5 million, but the damage la ... Read more
-
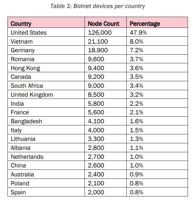
The Cyber Express
U.S. Intelligence Agencies Say Chinese Botnet Compromised 260,000 Devices
U.S. intelligence agencies issued a warning today about a Chinese botnet that has compromised 260,000 devices around the globe, including small office/home office (SOHO) routers, firewalls, network-at ... Read more

-
Cybersecurity News
166k+ Projects at Risk: AutoGPT’s Critical Vulnerability Explained – CVE-2024-6091 (CVSS 9.8)
A significant security vulnerability has been discovered in AutoGPT, a powerful AI tool designed to automate tasks through intelligent agents. With over 166k stars on GitHub, AutoGPT has gained popula ... Read more

-
Cybersecurity News
PAN-OS Vulnerabilities: Command Injection (CVE-2024-8686) and GlobalProtect Exposure (CVE-2024-8687)
Palo Alto Networks, a leading cybersecurity solutions provider, has recently released a critical security advisory, urging its customers to take immediate action to address several vulnerabilities dis ... Read more

-
Cybersecurity News
CVE-2024-42500 (CVSS 9.3): Critical HPE HP-UX Vulnerability Demands Immediate Action
A critical vulnerability has been discovered in HPE HP-UX’s Network File System (NFSv4), leaving systems open to potential denial-of-service (DoS) attacks. This vulnerability, tracked as CVE-2024-4250 ... Read more
The following table lists the changes that have been made to the
CVE-2024-4577 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Nov. 03, 2025
Action Type Old Value New Value Changed Reference Type PHP Group: https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv Types: Broken Link, Exploit, Third Party Advisory PHP Group: https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv Types: Exploit, Third Party Advisory Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-4577 Types: US Government Resource Changed Reference Type CVE: https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv Types: Broken Link, Exploit, Third Party Advisory CVE: https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv Types: Exploit, Third Party Advisory -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-4577 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-4577 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-4577 -
Reanalysis by [email protected]
Mar. 28, 2025
Action Type Old Value New Value Added CPE Configuration AND OR *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.2.0 up to (excluding) 8.2.20 *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.3.0 up to (excluding) 8.3.8 *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.1.0 up to (excluding) 8.1.29 OR cpe:2.3:o:microsoft:windows:-:*:*:*:*:*:*:* Removed CPE Configuration OR *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.2.0 up to (excluding) 8.2.20 *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.3.0 up to (excluding) 8.3.8 *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.1.0 up to (excluding) 8.1.29 -
Modified Analysis by [email protected]
Mar. 21, 2025
Action Type Old Value New Value Added Reference Type CVE: https://blog.talosintelligence.com/new-persistent-attacks-japan/ Types: Exploit, Third Party Advisory -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Mar. 14, 2025
Action Type Old Value New Value Added Reference https://blog.talosintelligence.com/new-persistent-attacks-japan/ -
Modified Analysis by [email protected]
Dec. 20, 2024
Action Type Old Value New Value Changed CPE Configuration OR *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 5.0.0 up to (excluding) 8.1.29 *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.2.0 up to (excluding) 8.2.20 *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.3.0 up to (excluding) 8.3.8 OR *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.1.0 up to (excluding) 8.1.29 *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.2.0 up to (excluding) 8.2.20 *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.3.0 up to (excluding) 8.3.8 Changed Reference Type http://www.openwall.com/lists/oss-security/2024/06/07/1 Mailing List, Release Notes http://www.openwall.com/lists/oss-security/2024/06/07/1 Mailing List, Third Party Advisory Changed Reference Type http://www.openwall.com/lists/oss-security/2024/06/07/1 Mailing List, Release Notes http://www.openwall.com/lists/oss-security/2024/06/07/1 Mailing List, Third Party Advisory Changed Reference Type https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv Broken Link https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv Exploit, Third Party Advisory Changed Reference Type https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv Broken Link https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv Exploit, Third Party Advisory Changed Reference Type https://github.com/rapid7/metasploit-framework/pull/19247 Exploit, Issue Tracking https://github.com/rapid7/metasploit-framework/pull/19247 Exploit, Issue Tracking, Patch Changed Reference Type https://github.com/rapid7/metasploit-framework/pull/19247 Exploit, Issue Tracking https://github.com/rapid7/metasploit-framework/pull/19247 Exploit, Issue Tracking, Patch Changed Reference Type https://lists.fedoraproject.org/archives/list/[email protected]/message/PKGTQUOA2NTZ3RXN22CSAUJPIRUYRB4B/ Mailing List, Third Party Advisory https://lists.fedoraproject.org/archives/list/[email protected]/message/PKGTQUOA2NTZ3RXN22CSAUJPIRUYRB4B/ Mailing List Changed Reference Type https://lists.fedoraproject.org/archives/list/[email protected]/message/PKGTQUOA2NTZ3RXN22CSAUJPIRUYRB4B/ Mailing List, Third Party Advisory https://lists.fedoraproject.org/archives/list/[email protected]/message/PKGTQUOA2NTZ3RXN22CSAUJPIRUYRB4B/ Mailing List Changed Reference Type https://lists.fedoraproject.org/archives/list/[email protected]/message/W45DBOH56NQDRTOM2DN2LNA2FZIMC3PK/ Mailing List, Third Party Advisory https://lists.fedoraproject.org/archives/list/[email protected]/message/W45DBOH56NQDRTOM2DN2LNA2FZIMC3PK/ Mailing List Changed Reference Type https://lists.fedoraproject.org/archives/list/[email protected]/message/W45DBOH56NQDRTOM2DN2LNA2FZIMC3PK/ Mailing List, Third Party Advisory https://lists.fedoraproject.org/archives/list/[email protected]/message/W45DBOH56NQDRTOM2DN2LNA2FZIMC3PK/ Mailing List Changed Reference Type https://www.vicarius.io/vsociety/posts/php-cgi-argument-injection-to-rce-cve-2024-4577 No Types Assigned https://www.vicarius.io/vsociety/posts/php-cgi-argument-injection-to-rce-cve-2024-4577 Exploit, Third Party Advisory Changed Reference Type https://www.vicarius.io/vsociety/posts/php-cgi-os-command-injection-vulnerability-cve-2024-4577 No Types Assigned https://www.vicarius.io/vsociety/posts/php-cgi-os-command-injection-vulnerability-cve-2024-4577 Exploit, Third Party Advisory -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference http://www.openwall.com/lists/oss-security/2024/06/07/1 Added Reference https://arstechnica.com/security/2024/06/php-vulnerability-allows-attackers-to-run-malicious-code-on-windows-servers/ Added Reference https://blog.orange.tw/2024/06/cve-2024-4577-yet-another-php-rce.html Added Reference https://cert.be/en/advisory/warning-php-remote-code-execution-patch-immediately Added Reference https://devco.re/blog/2024/06/06/security-alert-cve-2024-4577-php-cgi-argument-injection-vulnerability-en/ Added Reference https://github.com/11whoami99/CVE-2024-4577 Added Reference https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv Added Reference https://github.com/rapid7/metasploit-framework/pull/19247 Added Reference https://github.com/watchtowrlabs/CVE-2024-4577 Added Reference https://github.com/xcanwin/CVE-2024-4577-PHP-RCE Added Reference https://isc.sans.edu/diary/30994 Added Reference https://labs.watchtowr.com/no-way-php-strikes-again-cve-2024-4577/ Added Reference https://lists.fedoraproject.org/archives/list/[email protected]/message/PKGTQUOA2NTZ3RXN22CSAUJPIRUYRB4B/ Added Reference https://lists.fedoraproject.org/archives/list/[email protected]/message/W45DBOH56NQDRTOM2DN2LNA2FZIMC3PK/ Added Reference https://security.netapp.com/advisory/ntap-20240621-0008/ Added Reference https://www.imperva.com/blog/imperva-protects-against-critical-php-vulnerability-cve-2024-4577/ Added Reference https://www.php.net/ChangeLog-8.php#8.1.29 Added Reference https://www.php.net/ChangeLog-8.php#8.2.20 Added Reference https://www.php.net/ChangeLog-8.php#8.3.8 Added Reference https://www.vicarius.io/vsociety/posts/php-cgi-argument-injection-to-rce-cve-2024-4577 Added Reference https://www.vicarius.io/vsociety/posts/php-cgi-os-command-injection-vulnerability-cve-2024-4577 -
Modified Analysis by [email protected]
Aug. 14, 2024
Action Type Old Value New Value Changed Reference Type https://arstechnica.com/security/2024/06/php-vulnerability-allows-attackers-to-run-malicious-code-on-windows-servers/ Exploit, Third Party Advisory https://arstechnica.com/security/2024/06/php-vulnerability-allows-attackers-to-run-malicious-code-on-windows-servers/ Exploit, Press/Media Coverage, Third Party Advisory Changed Reference Type https://github.com/rapid7/metasploit-framework/pull/19247 Exploit https://github.com/rapid7/metasploit-framework/pull/19247 Exploit, Issue Tracking Changed Reference Type https://security.netapp.com/advisory/ntap-20240621-0008/ No Types Assigned https://security.netapp.com/advisory/ntap-20240621-0008/ Third Party Advisory -
CVE Modified by [email protected]
Jun. 21, 2024
Action Type Old Value New Value Added Reference PHP Group https://security.netapp.com/advisory/ntap-20240621-0008/ [No types assigned] -
Modified Analysis by [email protected]
Jun. 21, 2024
Action Type Old Value New Value Changed Reference Type http://www.openwall.com/lists/oss-security/2024/06/07/1 No Types Assigned http://www.openwall.com/lists/oss-security/2024/06/07/1 Mailing List, Release Notes Changed Reference Type https://lists.fedoraproject.org/archives/list/[email protected]/message/PKGTQUOA2NTZ3RXN22CSAUJPIRUYRB4B/ No Types Assigned https://lists.fedoraproject.org/archives/list/[email protected]/message/PKGTQUOA2NTZ3RXN22CSAUJPIRUYRB4B/ Mailing List, Third Party Advisory Changed Reference Type https://lists.fedoraproject.org/archives/list/[email protected]/message/W45DBOH56NQDRTOM2DN2LNA2FZIMC3PK/ No Types Assigned https://lists.fedoraproject.org/archives/list/[email protected]/message/W45DBOH56NQDRTOM2DN2LNA2FZIMC3PK/ Mailing List, Third Party Advisory Added CPE Configuration OR *cpe:2.3:o:fedoraproject:fedora:39:*:*:*:*:*:*:* *cpe:2.3:o:fedoraproject:fedora:40:*:*:*:*:*:*:* -
CVE Modified by [email protected]
Jun. 13, 2024
Action Type Old Value New Value Added Reference PHP Group https://lists.fedoraproject.org/archives/list/[email protected]/message/W45DBOH56NQDRTOM2DN2LNA2FZIMC3PK/ [No types assigned] -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Jun. 13, 2024
Action Type Old Value New Value Added Date Added 2024-06-12 Added Vulnerability Name PHP-CGI OS Command Injection Vulnerability Added Due Date 2024-07-03 Added Required Action Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable. -
CVE Modified by [email protected]
Jun. 12, 2024
Action Type Old Value New Value Added Reference PHP Group https://lists.fedoraproject.org/archives/list/[email protected]/message/PKGTQUOA2NTZ3RXN22CSAUJPIRUYRB4B/ [No types assigned] -
CVE Modified by [email protected]
Jun. 10, 2024
Action Type Old Value New Value Added Reference PHP Group http://www.openwall.com/lists/oss-security/2024/06/07/1 [No types assigned] -
CVE Modified by [email protected]
Jun. 10, 2024
Action Type Old Value New Value -
Initial Analysis by [email protected]
Jun. 10, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://arstechnica.com/security/2024/06/php-vulnerability-allows-attackers-to-run-malicious-code-on-windows-servers/ No Types Assigned https://arstechnica.com/security/2024/06/php-vulnerability-allows-attackers-to-run-malicious-code-on-windows-servers/ Exploit, Third Party Advisory Changed Reference Type https://blog.orange.tw/2024/06/cve-2024-4577-yet-another-php-rce.html No Types Assigned https://blog.orange.tw/2024/06/cve-2024-4577-yet-another-php-rce.html Third Party Advisory Changed Reference Type https://cert.be/en/advisory/warning-php-remote-code-execution-patch-immediately No Types Assigned https://cert.be/en/advisory/warning-php-remote-code-execution-patch-immediately Third Party Advisory Changed Reference Type https://devco.re/blog/2024/06/06/security-alert-cve-2024-4577-php-cgi-argument-injection-vulnerability-en/ No Types Assigned https://devco.re/blog/2024/06/06/security-alert-cve-2024-4577-php-cgi-argument-injection-vulnerability-en/ Exploit, Third Party Advisory Changed Reference Type https://github.com/11whoami99/CVE-2024-4577 No Types Assigned https://github.com/11whoami99/CVE-2024-4577 Exploit Changed Reference Type https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv No Types Assigned https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv Broken Link Changed Reference Type https://github.com/rapid7/metasploit-framework/pull/19247 No Types Assigned https://github.com/rapid7/metasploit-framework/pull/19247 Exploit Changed Reference Type https://github.com/watchtowrlabs/CVE-2024-4577 No Types Assigned https://github.com/watchtowrlabs/CVE-2024-4577 Exploit, Third Party Advisory Changed Reference Type https://github.com/xcanwin/CVE-2024-4577-PHP-RCE No Types Assigned https://github.com/xcanwin/CVE-2024-4577-PHP-RCE Exploit, Third Party Advisory Changed Reference Type https://isc.sans.edu/diary/30994 No Types Assigned https://isc.sans.edu/diary/30994 Exploit, Third Party Advisory Changed Reference Type https://labs.watchtowr.com/no-way-php-strikes-again-cve-2024-4577/ No Types Assigned https://labs.watchtowr.com/no-way-php-strikes-again-cve-2024-4577/ Exploit, Third Party Advisory Changed Reference Type https://www.imperva.com/blog/imperva-protects-against-critical-php-vulnerability-cve-2024-4577/ No Types Assigned https://www.imperva.com/blog/imperva-protects-against-critical-php-vulnerability-cve-2024-4577/ Third Party Advisory Changed Reference Type https://www.php.net/ChangeLog-8.php#8.1.29 No Types Assigned https://www.php.net/ChangeLog-8.php#8.1.29 Release Notes Changed Reference Type https://www.php.net/ChangeLog-8.php#8.2.20 No Types Assigned https://www.php.net/ChangeLog-8.php#8.2.20 Release Notes Changed Reference Type https://www.php.net/ChangeLog-8.php#8.3.8 No Types Assigned https://www.php.net/ChangeLog-8.php#8.3.8 Release Notes Added CWE NIST CWE-78 Added CPE Configuration OR *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 5.0.0 up to (excluding) 8.1.29 *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.2.0 up to (excluding) 8.2.20 *cpe:2.3:a:php:php:*:*:*:*:*:*:*:* versions from (including) 8.3.0 up to (excluding) 8.3.8 -
CVE Modified by [email protected]
Jun. 10, 2024
Action Type Old Value New Value Added Reference PHP Group https://cert.be/en/advisory/warning-php-remote-code-execution-patch-immediately [No types assigned] Added Reference PHP Group https://isc.sans.edu/diary/30994 [No types assigned] -
CVE Modified by [email protected]
Jun. 10, 2024
Action Type Old Value New Value Added Reference PHP Group https://blog.orange.tw/2024/06/cve-2024-4577-yet-another-php-rce.html [No types assigned] Added Reference PHP Group https://devco.re/blog/2024/06/06/security-alert-cve-2024-4577-php-cgi-argument-injection-vulnerability-en/ [No types assigned] Added Reference PHP Group https://arstechnica.com/security/2024/06/php-vulnerability-allows-attackers-to-run-malicious-code-on-windows-servers/ [No types assigned] Added Reference PHP Group https://www.imperva.com/blog/imperva-protects-against-critical-php-vulnerability-cve-2024-4577/ [No types assigned] Added Reference PHP Group https://github.com/11whoami99/CVE-2024-4577 [No types assigned] Added Reference PHP Group https://github.com/xcanwin/CVE-2024-4577-PHP-RCE [No types assigned] Added Reference PHP Group https://github.com/rapid7/metasploit-framework/pull/19247 [No types assigned] Added Reference PHP Group https://labs.watchtowr.com/no-way-php-strikes-again-cve-2024-4577/ [No types assigned] Added Reference PHP Group https://github.com/watchtowrlabs/CVE-2024-4577 [No types assigned] Added Reference PHP Group https://www.php.net/ChangeLog-8.php#8.1.29 [No types assigned] Added Reference PHP Group https://www.php.net/ChangeLog-8.php#8.2.20 [No types assigned] Added Reference PHP Group https://www.php.net/ChangeLog-8.php#8.3.8 [No types assigned] -
CVE Received by [email protected]
Jun. 09, 2024
Action Type Old Value New Value Added Description In PHP versions 8.1.* before 8.1.29, 8.2.* before 8.2.20, 8.3.* before 8.3.8, when using Apache and PHP-CGI on Windows, if the system is set up to use certain code pages, Windows may use "Best-Fit" behavior to replace characters in command line given to Win32 API functions. PHP CGI module may misinterpret those characters as PHP options, which may allow a malicious user to pass options to PHP binary being run, and thus reveal the source code of scripts, run arbitrary PHP code on the server, etc. Added Reference PHP Group https://github.com/php/php-src/security/advisories/GHSA-3qgc-jrrr-25jv [No types assigned] Added CWE PHP Group CWE-78 Added CVSS V3.1 PHP Group AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H