CVE-2024-38054
Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability
Description
Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability
INFO
Published Date :
July 9, 2024, 5:15 p.m.
Last Modified :
Nov. 21, 2024, 9:24 a.m.
Remotely Exploit :
No
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-38054
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Apply the latest security updates for your operating system.
- Reboot the system if prompted.
Public PoC/Exploit Available at Github
CVE-2024-38054 has a 2 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-38054.
| URL | Resource |
|---|---|
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38054 | Patch Vendor Advisory |
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38054 | Patch Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-38054 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-38054
weaknesses.
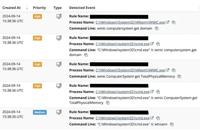
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
常用功能的DLL插件
Collection of Windows Privilege Escalation (Analyse/PoC/Exploit)
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-38054 vulnerability anywhere in the article.

-
TheCyberThrone
TheCyberThrone Security BiWeekly Review – December 14, 2024
Welcome to TheCyberThrone cybersecurity week in review will be posted covering the important security happenings. This review is for the weeks ending Saturday, November 30, 2024.Jenkins fixes multiple ... Read more

-
TheCyberThrone
Apache Arrow affected by CVE-2024-52338 Code Execution Flaw
The Apache Arrow R package has been identified with a critical security vulnerability impacting versions 4.0.0 through 16.1.0, could allow attackers to execute arbitrary code on systems processing ma ... Read more

-
TheCyberThrone
The CyberThrone Most Exploited Vulnerabilities Top 10 – November 2024
Welcome to TheCyberThrone most exploited vulnerabilities review. This review is for the month of November 2024CVE-2024-9463: Palo Alto OS Command InjectionCVSS 3.1 Score : 9.9 CISA KEV: YesThis vuln ... Read more

-
TheCyberThrone
TheCyberThrone CyberSecurity Newsletter Top 5 Articles – November, 2024
Welcome to TheCyberThrone cybersecurity month in review will be posted covering the important security happenings . This review is for the month ending November, 2024Subscribers favorite #1Apache Airf ... Read more

-
TheCyberThrone
AnyDesk affected by CVE-2024-52940
The open-source remote desktop software “Any Desk” has been affected by a vulnerability could allow attackers to uncover users’ IP addresses, posing significant privacy risks.The vulnerability tracked ... Read more

-
TheCyberThrone
PaloAlto devices are under massive exploitation
Researchers from Shadowserver have revealed that approximately 2,000 Palo Alto Networks firewalls have been compromised leavaraging recently discovered zeroday bugs. namely CVE-2024-0012 and CVE-2024 ... Read more
-
Cybersecurity News
Hackers Exploit Foundation Software, Exposing Sensitive Contractor Data
Attacker commands enumerating machine details | Image: HuntressRecently, the cybersecurity company Huntress reported a new wave of cyberattacks targeting the widely-used Foundation Accounting Software ... Read more

-
Cybersecurity News
CVE-2024-35783 (CVSS 9.4): Critical-Severity Flaw Exposes Siemens Industrial Systems
Siemens has issued a critical security advisory regarding a remote code execution (RCE) vulnerability in several of its SIMATIC products, including SIMATIC Process Historian, SIMATIC PCS 7, and SIMATI ... Read more

-
Cybersecurity News
Critical Cisco SLU Vulnerabilities CVE-2024-20439 and CVE-2024-20440 Threaten Remote Admin Control
Cisco has issued a security advisory warning organizations of multiple vulnerabilities in its Smart Licensing Utility (SLU) that could allow remote attackers to access sensitive information or gain ad ... Read more

-
Cybersecurity News
Windows 11 Surpasses Windows 10 as Dominant PC Gaming Platform
Please enable JavaScriptIn a notable development in the PC gaming landscape, Windows 11 has officially overtaken its predecessor, Windows 10, as the most widely adopted operating system among Steam us ... Read more

-
Cybersecurity News
CISA Warns of Actively Exploited Apache OFBiz CVE-2024-38856 Vulnerability, PoC Available
Image: securelayer7The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent warning about an actively exploited security flaw in Apache OFBiz, a popular open-source enterp ... Read more

-
Cybersecurity News
Chinese Hackers Deploy VersaMem Web Shell via Versa Director Zero-Day (CVE-2024-39717)
Overview of the Versa Director exploitation process and the VersaMem web shell functionalityBlack Lotus Labs, a threat intelligence team within Lumen Technologies, has uncovered the active exploitatio ... Read more

-
Cybersecurity News
Zero-Click Windows RCE Threat: Researcher Publishes PoC Exploit for CVE-2024-38063
In a significant development for cybersecurity professionals, security researcher Ynwarcs has published an in-depth analysis and proof-of-concept (PoC) exploit code for a critical zero-click CVE-2024- ... Read more

-
TheCyberThrone
GitHub fixes several vulnerabilities including CVE-2024-6800
GitHub has addressed several vulnerabilities in GitHub Enterprise Server (GHES) that could have allowed attackers to gain unauthorized access and manipulate repositories.The most critical vulnerabilit ... Read more

-
TheCyberThrone
PoC Exploit for Microsoft bug CVE-2024-38054 released
Security researcher ‘Frost’ has released proof-of-concept exploit code for the high-severity vulnerability in the Kernel Streaming WOW Thunk Service Driver could enable local attackers to escalate pri ... Read more

-
TheCyberThrone
Velvet Ant APT exploits Cisco bug CVE-2024-20399
Security researchers discovered that the China-linked APT group Velvet Ant has exploited the recently disclosed zero-day CVE-2024-20399 in Cisco switches to take over the network devices.Last month, C ... Read more

-
Cybersecurity News
Exploit for CVE-2024-38054 Released: Elevation of Privilege Flaw in Windows Kernel Streaming WOW Thunk
Security researcher ‘Frost’ has released proof-of-concept exploit code for the CVE-2024-38054 vulnerability, escalating concerns over a recently patched Windows security flaw. This high-severity vulne ... Read more
-
Cybersecurity News
CVE-2024-6800 (CVSS 9.5): Critical GitHub Enterprise Server Flaw Patched, Admin Access at Risk
GitHub, the world’s leading software development platform, has recently disclosed multiple security vulnerabilities in GitHub Enterprise Server (GHES) that could have allowed attackers to gain unautho ... Read more

-
tripwire.com
Tripwire Patch Priority Index for July 2024
Tripwire's July 2024 Patch Priority Index (PPI) brings together important vulnerabilities for Microsoft.First on the list are patches for Microsoft Office and Outlook that resolve remote code executio ... Read more
The following table lists the changes that have been made to the
CVE-2024-38054 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38054 -
Initial Analysis by [email protected]
Jul. 11, 2024
Action Type Old Value New Value Changed Reference Type https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38054 No Types Assigned https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38054 Patch, Vendor Advisory Added CWE NIST CWE-787 Added CPE Configuration OR *cpe:2.3:o:microsoft:windows_10_1507:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.10240.20710 *cpe:2.3:o:microsoft:windows_10_1607:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.14393.7159 *cpe:2.3:o:microsoft:windows_10_1809:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.6054 *cpe:2.3:o:microsoft:windows_10_21h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.19044.4651 *cpe:2.3:o:microsoft:windows_10_22h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.19045.4651 *cpe:2.3:o:microsoft:windows_11_21h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22000.3079 *cpe:2.3:o:microsoft:windows_11_22h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22621.3880 *cpe:2.3:o:microsoft:windows_11_23h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.22631.3880 *cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:x64:* *cpe:2.3:o:microsoft:windows_server_2012:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.14393.7159 *cpe:2.3:o:microsoft:windows_server_2019:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.6054 *cpe:2.3:o:microsoft:windows_server_2022:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.20348.2582 *cpe:2.3:o:microsoft:windows_server_2022_23h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.25398.1009 -
CVE Received by [email protected]
Jul. 09, 2024
Action Type Old Value New Value Added Description Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability Added Reference Microsoft Corporation https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38054 [No types assigned] Added CWE Microsoft Corporation CWE-122 Added CVSS V3.1 Microsoft Corporation AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H