CVE-2024-4872
Apache HTTP Server SQL Injection
Description
A vulnerability exists in the query validation of the MicroSCADA Pro/X SYS600 product. If exploited this could allow an authenticated attacker to inject code towards persistent data. Note that to successfully exploit this vulnerability an attacker must have a valid credential.
INFO
Published Date :
Aug. 27, 2024, 1:15 p.m.
Last Modified :
Oct. 30, 2024, 3:31 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-4872
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-4872.
| URL | Resource |
|---|---|
| https://publisher.hitachienergy.com/preview?DocumentID=8DBD000160&LanguageCode=en&DocumentPartId=&Action=Launch | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-4872 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-4872
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-4872 vulnerability anywhere in the article.

-
The Hacker News
⚡ Weekly Recap: Windows 0-Day, VPN Exploits, Weaponized AI, Hijacked Antivirus and More
Attackers aren't waiting for patches anymore — they are breaking in before defenses are ready. Trusted security tools are being hijacked to deliver malware. Even after a breach is detected and patched ... Read more

-
The Cyber Express
CISA’s Latest Advisories Expose High-Risk Vulnerabilities in Industrial Control Systems
The Cybersecurity and Infrastructure Security Agency (CISA) issued two crucial Industrial Control Systems (ICS) advisories, highlighting vulnerabilities that could have serious impacts on critical inf ... Read more

-
Cyber Security News
CISA Releases Two ICS Advisories for Vulnerabilities, & Exploits Surrounding ICS
The Cybersecurity and Infrastructure Security Agency (CISA) released two Industrial Control Systems (ICS) advisories on April 1, 2025, highlighting significant vulnerabilities in critical infrastructu ... Read more
-
Cybersecurity News
Threat Actors Exploit HR-Related Phishing Tactics in Sophisticated Credential-Stealing Campaigns
Image: CofensePhishing attacks continue to evolve in complexity, and the latest report from the Cofense Phishing Defense Center highlights a troubling trend: cybercriminals are increasingly using HR-r ... Read more

-
Cybersecurity News
The Safe C++ Extensions Proposal: Strengthening Security in a Complex Ecosystem
In a decisive move to address long-standing memory safety concerns, the C++ community has unveiled the Safe C++ Extensions proposal, marking a crucial moment for the language. After two years of in-de ... Read more
-
Cybersecurity News
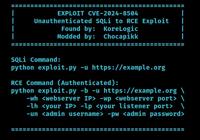
Critical Flaws Found in VICIdial Contact Center Suite: CVE-2024-8503 and CVE-2024-8504, PoC Published
In a concerning development for call centers using VICIdial, a popular open-source contact center solution, two high-severity security vulnerabilities have been discovered that could lead to severe da ... Read more
-
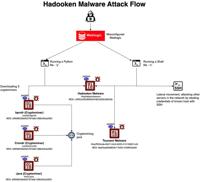
Cybersecurity News
Hadooken Malware: A New Threat to WebLogic Servers
The entire attack flow | Image: Aqua NautilusCybersecurity researchers at Aqua Nautilus have discovered a new Linux malware strain, dubbed “Hadooken,” that is specifically targeting Oracle WebLogic se ... Read more

-
Cybersecurity News
CVE-2024-45411: Twig Sandbox Bypass Vulnerability Puts PHP Applications at Risk
A critical security vulnerability has been discovered in Twig, a widely used PHP template engine, potentially allowing attackers to bypass sandbox restrictions and execute malicious code. The vulnerab ... Read more

-
Cybersecurity News
CVE-2024-6596 (CVSS 9.8): Critical Code Injection Flaw Found in Endress+Hauser Products
CERT@VDE coordinated with Endress+Hauser, a well-known leader in industrial automation and instrumentation, has issued a security advisory for a critical vulnerability (CVE-2024-6596) affecting severa ... Read more

-
Cybersecurity News
Microsoft’s September Patch Tuesday: A Patchwork of Urgency with 4 Zero-Days Under Attack
This September’s edition of Microsoft’s Patch Tuesday addresses 79 vulnerabilities, including 6 critical and 71 important severity issues. Among these, four zero-day vulnerabilities were actively expl ... Read more

-
Cybersecurity News
CVE-2024-38650 & CVE-2024-39714 (CVSS 9.9): Critical Flaws in Veeam Console Put Data at Risk
A series of critical vulnerabilities have been discovered in Veeam Service Provider Console, a widely-used platform for managing data protection services in cloud and virtual environments. These vulne ... Read more

-
Cybersecurity News
Windows 11 Surpasses Windows 10 as Dominant PC Gaming Platform
Please enable JavaScriptIn a notable development in the PC gaming landscape, Windows 11 has officially overtaken its predecessor, Windows 10, as the most widely adopted operating system among Steam us ... Read more

-
Cybersecurity News
Mekotio Trojan: A PowerShell-Based Threat Targeting Victims with Stealth and Persistence
The CYFIRMA Research and Advisory Team has identified a new and sophisticated cyber threat, dubbed the Mekotio Trojan. This malware leverages PowerShell, a powerful scripting language built into Windo ... Read more

-
Cybersecurity News
Critical Vulnerabilities Expose Hitachi Energy MicroSCADA X SYS600 to Cyberattacks
Hitachi Energy has issued a cybersecurity advisory addressing multiple critical vulnerabilities discovered in their MicroSCADA X SYS600 product, widely used for monitoring and controlling power system ... Read more

-
Cybersecurity News
CVE-2024-28000 in LiteSpeed Cache Plugin Actively Exploited: Over 30,000 Attacks Blocked in 24 Hours
A critical security vulnerability in the widely used LiteSpeed Cache plugin for WordPress has come under active exploitation, with over 30,000 attack attempts blocked in just the past 24 hours, accord ... Read more
The following table lists the changes that have been made to the
CVE-2024-4872 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 30, 2024
Action Type Old Value New Value Removed CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Added CVSS V3.1 NIST AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Removed CWE NIST CWE-89 Added CWE NIST NVD-CWE-Other Changed CPE Configuration OR *cpe:2.3:a:hitachienergy:microscada_x_sys600:*:*:*:*:*:*:*:* versions up to (excluding) 10.6 OR *cpe:2.3:a:hitachienergy:microscada_pro_sys600:9.4:fixpack_2_hf1:*:*:*:*:*:* *cpe:2.3:a:hitachienergy:microscada_pro_sys600:9.4:fixpack_2_hf2:*:*:*:*:*:* *cpe:2.3:a:hitachienergy:microscada_pro_sys600:9.4:fixpack_2_hf3:*:*:*:*:*:* *cpe:2.3:a:hitachienergy:microscada_pro_sys600:9.4:fixpack_2_hf4:*:*:*:*:*:* *cpe:2.3:a:hitachienergy:microscada_pro_sys600:9.4:fixpack_2_hf5:*:*:*:*:*:* *cpe:2.3:a:hitachienergy:microscada_x_sys600:*:*:*:*:*:*:*:* versions from (including) 10.0 up to (excluding) 10.6 -
CVE Modified by [email protected]
Oct. 29, 2024
Action Type Old Value New Value Changed Description The product does not validate any query towards persistent data, resulting in a risk of injection attacks. A vulnerability exists in the query validation of the MicroSCADA Pro/X SYS600 product. If exploited this could allow an authenticated attacker to inject code towards persistent data. Note that to successfully exploit this vulnerability an attacker must have a valid credential. -
CVE Modified by [email protected]
Sep. 05, 2024
Action Type Old Value New Value Added CWE Hitachi Energy CWE-943 -
CVE Modified by [email protected]
Aug. 30, 2024
Action Type Old Value New Value Removed CWE Hitachi Energy CWE-89 -
Initial Analysis by [email protected]
Aug. 28, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://publisher.hitachienergy.com/preview?DocumentID=8DBD000160&LanguageCode=en&DocumentPartId=&Action=Launch No Types Assigned https://publisher.hitachienergy.com/preview?DocumentID=8DBD000160&LanguageCode=en&DocumentPartId=&Action=Launch Vendor Advisory Added CWE NIST CWE-89 Added CPE Configuration OR *cpe:2.3:a:hitachienergy:microscada_x_sys600:*:*:*:*:*:*:*:* versions up to (excluding) 10.6 -
CVE Received by [email protected]
Aug. 27, 2024
Action Type Old Value New Value Added Description The product does not validate any query towards persistent data, resulting in a risk of injection attacks. Added Reference Hitachi ABB Power Grids https://publisher.hitachienergy.com/preview?DocumentID=8DBD000160&LanguageCode=en&DocumentPartId=&Action=Launch [No types assigned] Added CWE Hitachi ABB Power Grids CWE-89 Added CVSS V3.1 Hitachi ABB Power Grids AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H