CVE-2024-38816
CVE-2024-38816: Path traversal vulnerability in functional web frameworks
Description
Applications serving static resources through the functional web frameworks WebMvc.fn or WebFlux.fn are vulnerable to path traversal attacks. An attacker can craft malicious HTTP requests and obtain any file on the file system that is also accessible to the process in which the Spring application is running. Specifically, an application is vulnerable when both of the following are true: * the web application uses RouterFunctions to serve static resources * resource handling is explicitly configured with a FileSystemResource location However, malicious requests are blocked and rejected when any of the following is true: * the Spring Security HTTP Firewall https://docs.spring.io/spring-security/reference/servlet/exploits/firewall.html is in use * the application runs on Tomcat or Jetty
INFO
Published Date :
Sept. 13, 2024, 6:15 a.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-38816
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
No affected product recoded yet
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Upgrade Spring Framework to version 5.3.40, 6.0.24, or 6.1.13 or later.
- Update Atlassian Confluence to version 7.19.29, 8.5.17, 8.9.8, or 9.1.1 or later.
- Apply the appropriate patch from the January 2025 Oracle advisory.
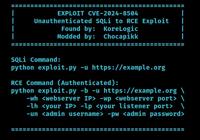
Public PoC/Exploit Available at Github
CVE-2024-38816 has a 35 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-38816.
| URL | Resource |
|---|---|
| https://spring.io/security/cve-2024-38816 | |
| https://security.netapp.com/advisory/ntap-20241227-0001/ |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-38816 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-38816
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
JAVA and Angular project about a CRM To manage permissions and productions
Java SCSS TypeScript HTML
Honeypot multi-servicio T-Pot CE desplegado 80 horas en DigitalOcean — análisis de +350,000 ataques reales, mitigación activa con iptables/ufw y threat intelligence.
None
Shell Python
None
A marketplace for claude plugins I've created.
Claude Code skill that analyzes and remediates CVE vulnerabilities in Java/Kotlin Spring Boot applications
AI 会话记录查看工具,支持 Claude Code 和 Codex
Shell Swift Python
None
Java
备份的漏洞库,3月开始我们来维护
None
None
Smith: It's a security Agent Written with Scala 3.x
Scala Shell
None
HTML
Fork spring-webmvc 5.3.39 to fix CVE-2024-38816, CVE-2024-38819
Java Kotlin FreeMarker
wy876
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-38816 vulnerability anywhere in the article.

-
The Cyber Express
Cyble Sensors Uncover Cyberattacks on Java Framework and IoT Devices
Cyble vulnerability intelligence unit has shared a report, detailing the recent cyberattacks on the Spring Java framework and hundreds of thousands of Internet of Things (IoT) devices. The report shed ... Read more

-
Cybersecurity News
PoC Exploit Releases for CVE-2024-44193: Local Privilege Escalation Vulnerability in iTunes
Image: mbog14 Security researcher mbog14 has published the technical details and proof-of-concept for a critical local privilege escalation (LPE) vulnerability affecting iTunes version 12.13.2.3, iden ... Read more

-
TheCyberThrone
TheCyberThrone Security Week In Review – September 21, 2024
Welcome to TheCyberThrone cybersecurity week in review will be posted covering the important security happenings. This review is for the week ending Saturday, September 21, 2024.Microsoft Kernel Vulne ... Read more

-
TheCyberThrone
Atlassian fixes DoS vulnerabilities in its Products
Atlassian releases patches for high-severity vulnerabilities in Bamboo, Bitbucket, Confluence, and Crowd.There are four vulnerabilities addressed in these products, all four allowing attackers to caus ... Read more

-
TheCyberThrone
Microsoft Kernel Vulnerability CVE-2024-37985 exploited
Microsoft has confirmed the exploitation of a Windows Kernel vulnerability, identified as CVE-2024-37985, in the wild.This vulnerability, first released on July 9, 2024, and last updated on September ... Read more

-
Cybersecurity News
CISA Warns of Actively Exploited Apache, Microsoft, and Oracle Vulnerabilities
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning to federal agencies and organizations worldwide: five newly identified security vulnerabilities are being actively ... Read more

-
TheCyberThrone
Google Chrome 129 released with several bug fixes
Google has released Chrome 129, with bug fixes for several vulnerabilities, which are now available on the stable channel for Windows, Mac, and Linux users.The new version release addresses nine vulne ... Read more

-
TheCyberThrone
CISA KEV Update September 2024 -Part V
The US CISA adds two vulnerabilities to its Known Exploited Vulnerabilities Catalog based on the evidence of active exploitationThe first vulnerability tracked as CVE-2024-43461, Microsoft Windows MSH ... Read more
-
Cybersecurity News
Critical Flaws Found in VICIdial Contact Center Suite: CVE-2024-8503 and CVE-2024-8504, PoC Published
In a concerning development for call centers using VICIdial, a popular open-source contact center solution, two high-severity security vulnerabilities have been discovered that could lead to severe da ... Read more
The following table lists the changes that have been made to the
CVE-2024-38816 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Mar. 18, 2025
Action Type Old Value New Value Added CWE CWE-22 -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Dec. 27, 2024
Action Type Old Value New Value Added Reference https://security.netapp.com/advisory/ntap-20241227-0001/ -
CVE Received by [email protected]
Sep. 13, 2024
Action Type Old Value New Value Added Description Applications serving static resources through the functional web frameworks WebMvc.fn or WebFlux.fn are vulnerable to path traversal attacks. An attacker can craft malicious HTTP requests and obtain any file on the file system that is also accessible to the process in which the Spring application is running. Specifically, an application is vulnerable when both of the following are true: * the web application uses RouterFunctions to serve static resources * resource handling is explicitly configured with a FileSystemResource location However, malicious requests are blocked and rejected when any of the following is true: * the Spring Security HTTP Firewall https://docs.spring.io/spring-security/reference/servlet/exploits/firewall.html is in use * the application runs on Tomcat or Jetty Added Reference VMware https://spring.io/security/cve-2024-38816 [No types assigned] Added CVSS V3.1 VMware AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N