CVE-2024-44000
WordPress LiteSpeed Cache plugin < 6.5.0.1 - Unauthenticated Account Takeover via Cookie Leak vulnerability
Description
Insufficiently Protected Credentials vulnerability in LiteSpeed Technologies LiteSpeed Cache litespeed-cache allows Authentication Bypass.This issue affects LiteSpeed Cache: from n/a through < 6.5.0.1.
INFO
Published Date :
Oct. 20, 2024, 12:15 p.m.
Last Modified :
April 23, 2026, 3:18 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Update the 'LiteSpeed Cache' plugin to version 6.5.0.1 or later through the administrative dashboard.
Public PoC/Exploit Available at Github
CVE-2024-44000 has a 8 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-44000.
| URL | Resource |
|---|---|
| https://patchstack.com/database/Wordpress/Plugin/litespeed-cache/vulnerability/wordpress-litespeed-cache-plugin-6-5-0-1-unauthenticated-account-takeover-vulnerability?_s_id=cve |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-44000 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-44000
weaknesses.
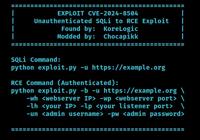
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
None
TypeScript CSS JavaScript
Ayato Hardening v2
Shell Python HCL HTML
GenCookieSessionHijack 是一个用于利用不安全暴露的 WordPress 调试日志并提取会话 Cookie 的 PoC 工具。通过该工具,攻击者可以劫持活跃的管理员会话,从而未授权地访问 WordPress 管理控制台。
cve poc wordpress
Python
is a PoC tool designed to exploit insecurely exposed debug logs from WordPress sites and extract session cookies
Python
CVE-2024-44000-LiteSpeed-Cache
Python
LiteSpeed Unauthorized Account Takeover
Python
CVE-2024-44000 is a vulnerability in the LiteSpeed Cache plugin, a popular WordPress plugin. This vulnerability affects session management in LiteSpeed Cache, allowing attackers to gain unauthorized access to sensitive data.
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-44000 vulnerability anywhere in the article.

-
The Cyber Express
Cyble Warns of Escalating Cyber Risks in IoT and WordPress Plugins Amid Phishing Surge
In the latest edition of Cyble’s weekly sensor intelligence report, cybersecurity experts revealed a concerning surge in attacks targeting the LightSpeed Cache and GutenKit WordPress plugins. As the r ... Read more

-
BleepingComputer
LiteSpeed Cache WordPress plugin bug lets hackers get admin access
The free version of the popular WordPress plugin LiteSpeed Cache has fixed a dangerous privilege elevation flaw on its latest release that could allow unauthenticated site visitors to gain admin right ... Read more

-
The Hacker News
LiteSpeed Cache Plugin Vulnerability Poses Significant Risk to WordPress Websites
Vulnerability / Website Security A high-severity security flaw has been disclosed in the LiteSpeed Cache plugin for WordPress that could allow an unauthenticated threat actor to elevate their privileg ... Read more

-
The Hacker News
WordPress LiteSpeed Cache Plugin Security Flaw Exposes Sites to XSS Attacks
Website Security / Vulnerability A new high-severity security flaw has been disclosed in the LiteSpeed Cache plugin for WordPress that could enable malicious actors to execute arbitrary JavaScript cod ... Read more
-
Cybersecurity News
Threat Actors Exploit HR-Related Phishing Tactics in Sophisticated Credential-Stealing Campaigns
Image: CofensePhishing attacks continue to evolve in complexity, and the latest report from the Cofense Phishing Defense Center highlights a troubling trend: cybercriminals are increasingly using HR-r ... Read more

-
Cybersecurity News
The Safe C++ Extensions Proposal: Strengthening Security in a Complex Ecosystem
In a decisive move to address long-standing memory safety concerns, the C++ community has unveiled the Safe C++ Extensions proposal, marking a crucial moment for the language. After two years of in-de ... Read more
-
Cybersecurity News
Critical Flaws Found in VICIdial Contact Center Suite: CVE-2024-8503 and CVE-2024-8504, PoC Published
In a concerning development for call centers using VICIdial, a popular open-source contact center solution, two high-severity security vulnerabilities have been discovered that could lead to severe da ... Read more
-
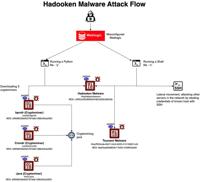
Cybersecurity News
Hadooken Malware: A New Threat to WebLogic Servers
The entire attack flow | Image: Aqua NautilusCybersecurity researchers at Aqua Nautilus have discovered a new Linux malware strain, dubbed “Hadooken,” that is specifically targeting Oracle WebLogic se ... Read more

-
Cybersecurity News
CVE-2024-45411: Twig Sandbox Bypass Vulnerability Puts PHP Applications at Risk
A critical security vulnerability has been discovered in Twig, a widely used PHP template engine, potentially allowing attackers to bypass sandbox restrictions and execute malicious code. The vulnerab ... Read more

-
Cybersecurity News
CVE-2024-6596 (CVSS 9.8): Critical Code Injection Flaw Found in Endress+Hauser Products
CERT@VDE coordinated with Endress+Hauser, a well-known leader in industrial automation and instrumentation, has issued a security advisory for a critical vulnerability (CVE-2024-6596) affecting severa ... Read more

-
Cybersecurity News
Microsoft’s September Patch Tuesday: A Patchwork of Urgency with 4 Zero-Days Under Attack
This September’s edition of Microsoft’s Patch Tuesday addresses 79 vulnerabilities, including 6 critical and 71 important severity issues. Among these, four zero-day vulnerabilities were actively expl ... Read more

-
Cybersecurity News
CVE-2024-45076 (CVSS 9.9): Critical Flaw in IBM webMethods Integration Demand Immediate Action
IBM has issued a critical security advisory for its webMethods Integration Server, revealing multiple vulnerabilities that could allow authenticated users to execute arbitrary commands, escalate privi ... Read more

-
security.nl
Miljoenen WordPress-sites kwetsbaar door kritiek lek in LiteSpeed Cache
Miljoenen WordPress-sites lopen door een kritieke kwetsbaarheid in de plug-in LiteSpeed Cache het risico op aanvallen. Een update is beschikbaar, maar die is door de meeste websites nog niet geïnstall ... Read more

-
The Hacker News
Critical Security Flaw Found in LiteSpeed Cache Plugin for WordPress
WordPress / Webinar Security Cybersecurity researchers have discovered yet another critical security flaw in the LiteSpeed Cache plugin for WordPress that could allow unauthenticated users to take con ... Read more

-
BleepingComputer
LiteSpeed Cache bug exposes 6 million WordPress sites to takeover attacks
Yet, another critical severity vulnerability has been discovered in LiteSpeed Cache, a caching plugin for speeding up user browsing in over 6 million WordPress sites. The flaw, tracked as CVE-2024-440 ... Read more

-
Cybersecurity News
CVE-2024-44000 (CVSS 9.8): Litespeed Cache flaw exposes millions of WordPress sites to takeover attacks
A significant security vulnerability has been uncovered in the popular LiteSpeed Cache plugin for WordPress, which boasts over 5 million active installations. The vulnerability, discovered by Rafie Mu ... Read more
The following table lists the changes that have been made to the
CVE-2024-44000 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by [email protected]
Apr. 23, 2026
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H -
CVE Modified by [email protected]
Apr. 01, 2026
Action Type Old Value New Value Changed Description Insufficiently Protected Credentials vulnerability in LiteSpeed Technologies LiteSpeed Cache allows Authentication Bypass.This issue affects LiteSpeed Cache: from n/a before 6.5.0.1. Insufficiently Protected Credentials vulnerability in LiteSpeed Technologies LiteSpeed Cache litespeed-cache allows Authentication Bypass.This issue affects LiteSpeed Cache: from n/a through < 6.5.0.1. Removed CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Added Reference https://patchstack.com/database/Wordpress/Plugin/litespeed-cache/vulnerability/wordpress-litespeed-cache-plugin-6-5-0-1-unauthenticated-account-takeover-vulnerability?_s_id=cve Removed Reference https://patchstack.com/articles/critical-account-takeover-vulnerability-patched-in-litespeed-cache-plugin?_s_id=cve Removed Reference https://patchstack.com/database/vulnerability/litespeed-cache/wordpress-litespeed-cache-plugin-6-5-0-1-unauthenticated-account-takeover-vulnerability?_s_id=cve Removed Reference Type https://patchstack.com/articles/critical-account-takeover-vulnerability-patched-in-litespeed-cache-plugin?_s_id=cve Types: Exploit, Third Party Advisory Removed Reference Type https://patchstack.com/database/vulnerability/litespeed-cache/wordpress-litespeed-cache-plugin-6-5-0-1-unauthenticated-account-takeover-vulnerability?_s_id=cve Types: Third Party Advisory -
Initial Analysis by [email protected]
Oct. 23, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://patchstack.com/articles/critical-account-takeover-vulnerability-patched-in-litespeed-cache-plugin?_s_id=cve No Types Assigned https://patchstack.com/articles/critical-account-takeover-vulnerability-patched-in-litespeed-cache-plugin?_s_id=cve Exploit, Third Party Advisory Changed Reference Type https://patchstack.com/database/vulnerability/litespeed-cache/wordpress-litespeed-cache-plugin-6-5-0-1-unauthenticated-account-takeover-vulnerability?_s_id=cve No Types Assigned https://patchstack.com/database/vulnerability/litespeed-cache/wordpress-litespeed-cache-plugin-6-5-0-1-unauthenticated-account-takeover-vulnerability?_s_id=cve Third Party Advisory Added CPE Configuration OR *cpe:2.3:a:litespeedtech:litespeed_cache:*:*:*:*:*:wordpress:*:* versions up to (excluding) 6.5.0.1 -
CVE Received by [email protected]
Oct. 20, 2024
Action Type Old Value New Value Added Description Insufficiently Protected Credentials vulnerability in LiteSpeed Technologies LiteSpeed Cache allows Authentication Bypass.This issue affects LiteSpeed Cache: from n/a before 6.5.0.1. Added Reference Patchstack https://patchstack.com/database/vulnerability/litespeed-cache/wordpress-litespeed-cache-plugin-6-5-0-1-unauthenticated-account-takeover-vulnerability?_s_id=cve [No types assigned] Added Reference Patchstack https://patchstack.com/articles/critical-account-takeover-vulnerability-patched-in-litespeed-cache-plugin?_s_id=cve [No types assigned] Added CWE Patchstack CWE-522 Added CVSS V3.1 Patchstack AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H