CVE-2024-38200
Microsoft Office Spoofing Vulnerability
Description
Microsoft Office Spoofing Vulnerability
INFO
Published Date :
Aug. 12, 2024, 1:38 p.m.
Last Modified :
Aug. 13, 2024, 6:15 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-38200
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | MEDIUM | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Ensure automatic updates are enabled for Microsoft Office applications.
- Manually update Microsoft Office to address the vulnerability.
Public PoC/Exploit Available at Github
CVE-2024-38200 has a 3 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-38200.
| URL | Resource |
|---|---|
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38200 | Patch Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-38200 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-38200
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
PoC on how Office 365 handles some files.
assembler assembly-language exploit exploitation javascript logic poc 2024 hacktoberfest hacktoberfest-accepted
Assembly JavaScript
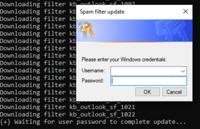
CVE-2024-38200 & CVE-2024-43609 - Microsoft Office NTLMv2 Disclosure Vulnerability
HTML Python
TOP All bugbounty pentesting CVE-2023- POC Exp RCE example payload Things
bugbounty cve exp exploit payload poc rce vulnerability
Shell
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-38200 vulnerability anywhere in the article.

-
Help Net Security
Microsoft vulnerabilities: What’s improved, what’s at risk
Microsoft reported a record 1,360 vulnerabilities in 2024, according to the latest BeyondTrust Microsoft Vulnerabilities Report. The volume marks an 11% increase from the previous record in 2022 and f ... Read more
-
Cybersecurity News
PythonRatLoader: The Malware Loader That’s Turning Phishing Into a Multi-Stage Attack
Attack Flow | Image: CofenseA recent report by Adam Martin and Kian Buckley Maher from the Cofense Phishing Defense Center (PDC) has revealed a sophisticated malware loader, PythonRatLoader, that is b ... Read more

-
Cybersecurity News
Chrome Patches Multi Vulnerabilities in Latest Stable Release
Google has rolled out a crucial update to its Chrome browser, addressing three high-severity security flaws that could be exploited by attackers. The update, versions 130.0.6723.69/.70 for Windows and ... Read more

-
Cybersecurity News
HORUS Protector: The New Undetectable Malware Crypter Threatening Cybersecurity
In a recent discovery by the SonicWall Capture Labs threat research team, a new malware crypter known as “HORUS Protector” has emerged, presenting a significant threat to cybersecurity defenses. This ... Read more

-
TheCyberThrone
Cisco reveals no patch available for CVE-2024-20393 and CVE-2024-20470
Cisco has revealed multiple vulnerabilities impacting its Small Business RV340, RV340W, RV345, and RV345P Dual WAN Gigabit VPN Routers, which could potentially expose businesses to serious security r ... Read more

-
TheCyberThrone
Apple fixes critical bugs in iOS 18
If you have any Apple devices running iOS 18, then make sure they have the latest patches installed.Apple has released an urgent iOS 18.0.1 and iPadOS 18.0.1 updates to fix two vulnerabilities, respec ... Read more

-
TheCyberThrone
PoC for Microsoft Office Zeroday CVE-2024-38200 released
Security researcher Metin Yunus Kandemir have released the technical details and a PoC exploit that reveals a critical information disclosure flaw in Microsoft Office. This vulnerability, which affect ... Read more

-
The Cyber Express
The Week’s Top Vulnerabilities: Cyble Urges Fixes for NVIDIA, Adobe, CUPS
Cyble researchers had a busy week, investigating 19 vulnerabilities in the week ended Oct.1 and flagging eight of them as high priority. Cyble’s weekly IT vulnerability report also noted that research ... Read more

-
Cybersecurity News
Prince Ransomware Hits UK and US via Royal Mail Phishing Scam
PDF containing a Dropbox URL | Image: Proofpoint Cybersecurity researchers at Proofpoint have uncovered a new phishing campaign that impersonates the British postal service, Royal Mail, to distribute ... Read more

-
Cybersecurity News
0-Day Flaw CVE-2024-38200 in Microsoft Office Exposes NTLMv2 Hashes: PoC Exploit Released
A discovered zero-day vulnerability is putting Microsoft Office users at risk. Security researcher Metin Yunus Kandemir recently published the technical details and a proof-of-concept (PoC) exploit th ... Read more

-
Cybersecurity News
Earth Preta’s Cyber Arsenal Expands: New Malware and Strategies Target APAC Governments
A new report from Trend Micro has revealed that Earth Preta, the notorious cyber espionage group, has significantly evolved its tactics and malware arsenal, posing a heightened threat to government en ... Read more

-
Cybersecurity News
CVE-2024-8517: Critical SPIP Flaw Leaves Websites Vulnerable to Remote Attacks, PoC Published
The popular open-source content management system (CMS), SPIP, is facing a critical security vulnerability that could allow unauthenticated attackers to execute malicious code on affected servers. The ... Read more

-
Cybersecurity News
HAProxy Vulnerability CVE-2024-45506 Under Active Exploit: Urgent Patching Required
In the latest security advisory, HAProxy revealed that CVE-2024-45506, a vulnerability in its popular load balancing and proxy software, is now actively exploited. The vulnerability, which has a CVSS ... Read more

-
europa.eu
Cyber Brief 24-09 - August 2024
Cyber Brief (August 2024)September 4, 2024 - Version: 1.0TLP:CLEARExecutive summaryWe analysed 249 open source reports for this Cyber Brief1.Relating to cyber policy and law enforcement, in Europe, th ... Read more

-
tripwire.com
Tripwire Patch Priority Index for August 2024
Tripwire's August 2024 Patch Priority Index (PPI) brings together important vulnerabilities for Microsoft, Adobe and Google.First on the list are patches for Microsoft Edge and Google Chromium that re ... Read more

-
Cybersecurity News
PoC Exploit Released for Arbitrary File Write Flaw (CVE-2024-22263) in Spring Cloud Data Flow
Security researcher Zeyad Azima from SecureLayer7 published the proof-of-concept exploit for arbitrary file write vulnerability (CVE-2024-22263) in Spring Cloud Data Flow, a widely-used tool for cloud ... Read more

-
Cybersecurity News
CVE-2024-31214 & CVE-2024-24809: Traccar Users Urged to Update Immediately
Image: Horizon3Please enable JavaScriptTwo critical vulnerabilities have been discovered in the popular GPS tracking system Traccar, which is used for both personal and corporate applications. The vul ... Read more

-
Cybersecurity News
PoC Exploit Released for RCE 0-day CVE-2024-41992 in Arcadyan FMIMG51AX000J Model
A critical vulnerability, identified as CVE-2024-41992, has been discovered in the Arcadyan FMIMG51AX000J model, and potentially other WiFi Alliance-affiliated devices using the same firmware version ... Read more

-
Help Net Security
Week in review: MS Office flaw may leak NTLM hashes, malicious Chrome, Edge browser extensions
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Unpatched MS Office flaw may leak NTLM hashes to attackers (CVE-2024-38200) A new MS Office zero-day v ... Read more
-
Cybersecurity News
Cybercriminals Evolve Social Engineering Tactics, Exploit CVE-2022-26923 in Sophisticated Campaign
Credential harvester prompt spawned by `AntiSpam.exe | Image: Rapid7 Recently, cybersecurity firm Rapid7 identified a series of sophisticated intrusion attempts linked to an ongoing social engineering ... Read more
The following table lists the changes that have been made to the
CVE-2024-38200 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by [email protected]
Aug. 13, 2024
Action Type Old Value New Value Removed CVSS V3.1 Microsoft Corporation AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N Added CVSS V3.1 Microsoft Corporation AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N -
Initial Analysis by [email protected]
Aug. 13, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:N Changed Reference Type https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38200 No Types Assigned https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38200 Patch, Vendor Advisory Added CWE NIST NVD-CWE-noinfo Added CPE Configuration OR *cpe:2.3:a:microsoft:365_apps:-:*:*:*:enterprise:*:x64:* *cpe:2.3:a:microsoft:365_apps:-:*:*:*:enterprise:*:x86:* *cpe:2.3:a:microsoft:office:2016:*:*:*:*:*:x64:* *cpe:2.3:a:microsoft:office:2016:*:*:*:*:*:x86:* *cpe:2.3:a:microsoft:office:2019:*:*:*:*:*:x64:* *cpe:2.3:a:microsoft:office:2019:*:*:*:*:*:x86:* *cpe:2.3:a:microsoft:office_long_term_servicing_channel:2021:*:*:*:*:*:x64:* *cpe:2.3:a:microsoft:office_long_term_servicing_channel:2021:*:*:*:*:*:x86:* -
CVE Received by [email protected]
Aug. 12, 2024
Action Type Old Value New Value Added Description Microsoft Office Spoofing Vulnerability Added Reference Microsoft Corporation https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38200 [No types assigned] Added CWE Microsoft Corporation CWE-200 Added CVSS V3.1 Microsoft Corporation AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N